Charlie Miller, a security expert who managed to jailbreak iOS 4.3 during the Pwn2Own hacking contest, has revealed an interesting piece of information about 4.3.1. According to Mr. Miller, the Safari exploit uncovered at Pwn2Own is still un-patched in Apple’s latest build of iOS.
An official jailbreak has yet to be released for 4.3.1, but the fact that this obvious exploit still exists points to the possibility of a jailbreak solution similar to JailbreakMe. There is no concrete evidence that this bug will be used in a jailbreak tool for iOS 4.3.1…
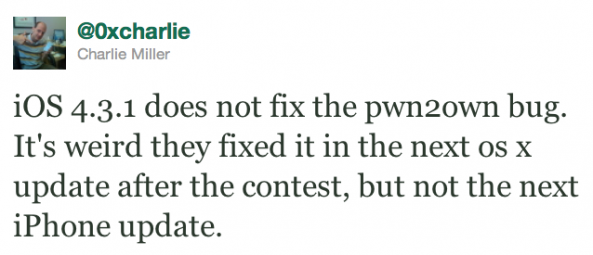
This specific exploit was present in Safari on the Mac and Mobile Safari for iOS. In the 10.6.7 update for OS X, Apple patched the exploit. In iOS 4.3.1, the bug still exists.
iClarified explains the exploit,
“The attack simply required that the target iPhone surfs to a rigged web site. On first attempt at the drive-by exploit, the iPhone browser crashed but once it was relaunched, Miller was able to hijack the entire address book.”
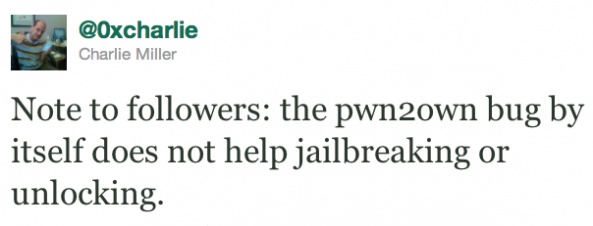
Charlie Miller does point out that this exploit does not mean anything for jailbreaking or unlocking by itself. It would only help with providing a method for a jailbreak solution.
This bug could mean that comex’s next jailbreak tool will work very similarly to the JailbreakMe website. Or it could mean that Apple will push out a 4.3.2 build of iOS to fix the exploit.
What do you think this exploit could mean for jailbreaking? Will we see a web-based tool like JailbreakMe in the near future? Only time will tell.
[iSpazio]
