Prosecutors in Germany are using data culled from Apple’s Health app in a rape and murder investigation, Motherboard reported Thursday citing German outlet Welt.
Afghan refugee Hussein K., who allegedly raped and murdered a 19-year-old student and disposed of her body in a river, has been on trial in Frieburg, Germany since September.
He refused to give investigators his iPhone’s passcode so they hired a Munich company to gain access to the device. The report does not mention the iPhone model the defendant was using or the name of the company that has helped authorities cracked the phone.
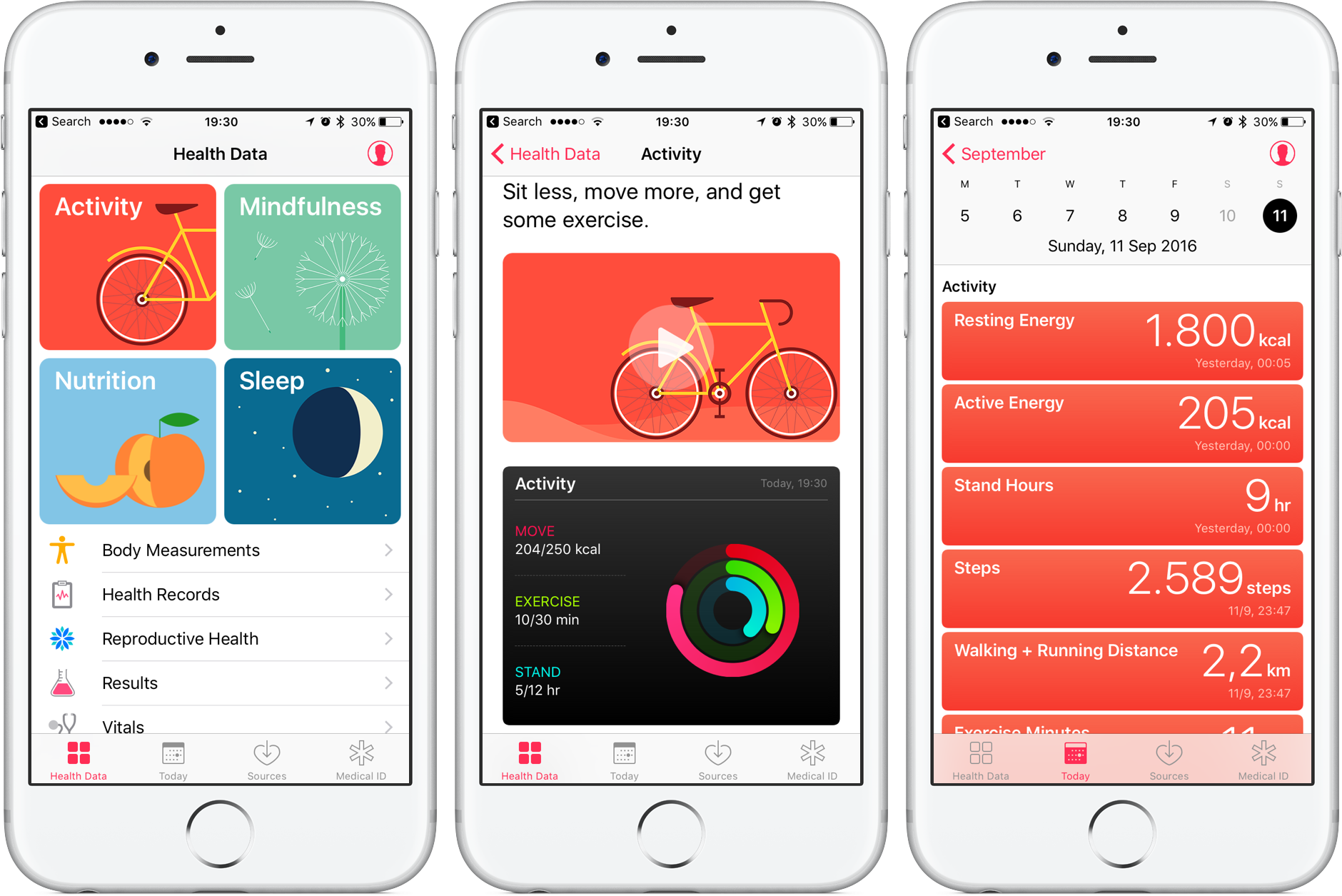
Investigators were able to glean Hussein’s whereabouts and what he was up to that day from information saved in the Health app on his iPhone.
Here’s an excerpt from the report:
The app records how many steps he took and what kind of activity he was doing throughout that day. The app recorded a portion of his activity as ‘climbing stairs,’ which authorities were able to correlate with the time he would have dragged his victim down the river embankment, and then climbed back up.
Freiburg police sent an investigator to the scene to replicate his movements, and sure enough, his Health app activity correlated with what was recorded on the defendant’s phone.
iPhones with a motion coprocessor embedded into the main A-series chip (all models from iPhone 5s onward) automatically track and save steps taken into the Health app. iPhones from iPhone 6 onward also automatically track elevation gain via the barometer sensor.
Although Health data is encrypted and inaccessible when the phone is locked, it’s available when you unlock the device (the app lacks password/Touch ID/Face ID protection).
TUTORIAL: How to sync Health database across multiple iPhones
According to Apple, Health app data is only stored on the device and encrypted with your passcode. If you choose to store your Health data in iCloud, it’s kept encrypted on Apple’s servers and also gets encrypted as it goes between iCloud and your device.
Health data is included in your iOS device backups when using iCloud Backup or backing up your iPhone in your computer by encrypting your iTunes backup.
Speaking of security, Motherboard in a separate story reported that FBI’s forensic expert Stephen Flatley called Apple “jerks” and “evil geniuses” for using strong encryption.