Well-known iOS jailbreak developer and hacker Majd Alfhaily was intrigued when read about MDSec’s black box hardware brute force for iOS devices. The tool, which runs over a USB connection, tries every possible passcode combination in an attempt to unlock an iPhone secured with a simple passcode.
The downside of such a tool, is that each PIN entry takes approximately 40 seconds, so it could take more than 110 hours to brute force an iPhone. Majd, being the curious person that he is, devised a way to do it in a fraction of the time using only software. The only caveat, if you even want to call it that given what it does, is that the device must be able to run unsigned code, i.e., the device must be jailbroken.
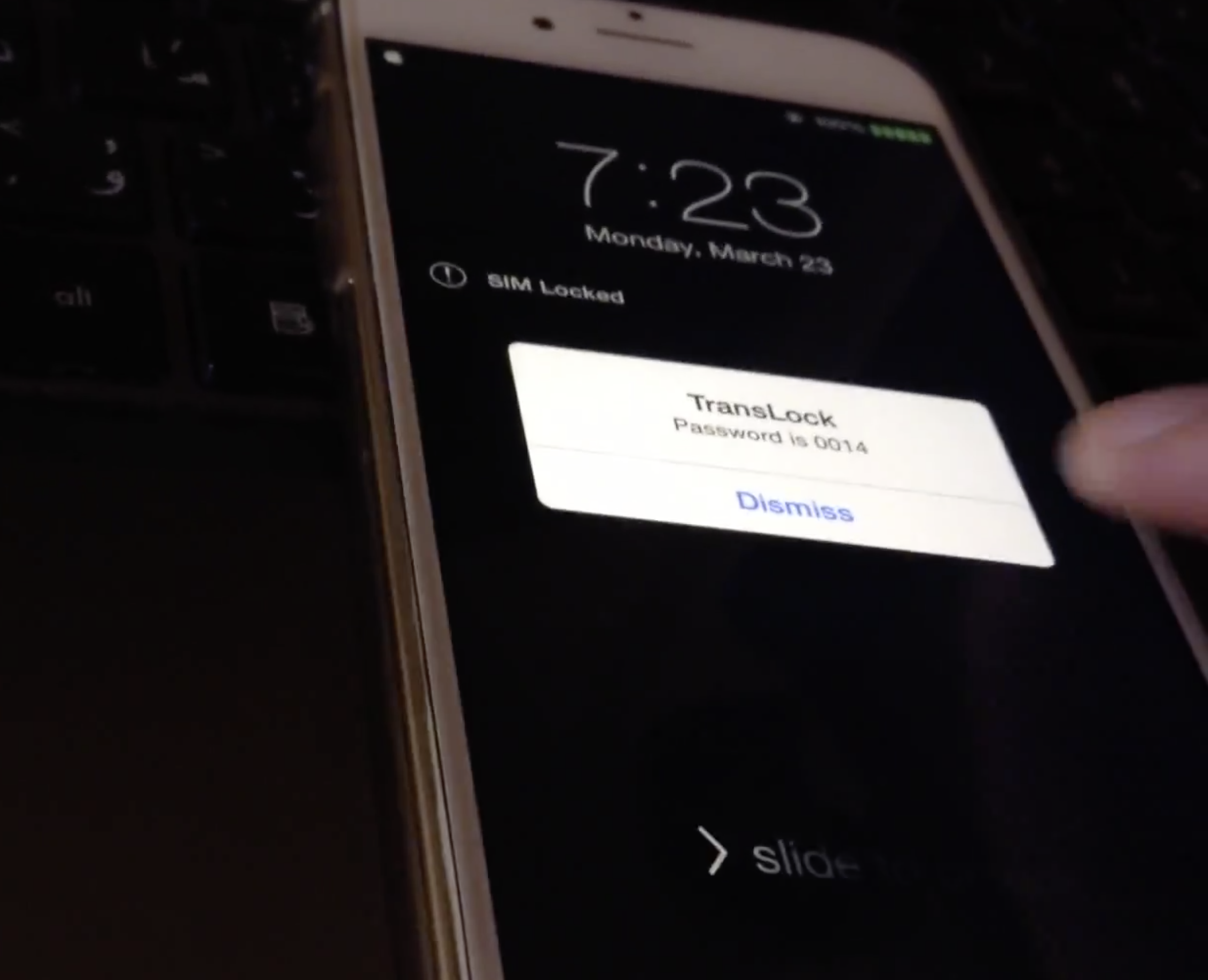
Majd’s tool would only take about 14 hours to try all possible passcode combinations 0000 through 9999. This is because he’s coded his tool in such a way that the device doesn’t disable after 10 bad passcode attempts, and it only requires five seconds instead of 40 seconds between each new attempt.
Although we certainly would not condone the usage of a tool like this for unscrupulous reasons, it’s a very interesting read, and the way Alfhaily pulls it off is pretty impressive. Watch the video above to see an example of his code in action.
Indeed, this tool is eye-opening, but it doesn’t mean that your iPhone is in imminent danger of being hacked. Consider these reasons:
- Non-jailbroken iPhones are not susceptible to this hack, since it requires running unsigned code
- A person would have to have physical access to your device to perform the hack
- A complex passcode would exponentially increase the security of your device, and renders the tool (in its current state) useless
In my opinion, the best thing that you can do to protect yourself is to use a complex passcode if you’re really worried about the security of your device. While a complex passcode is definitely not infallible, it certainly helps.
What do you think?