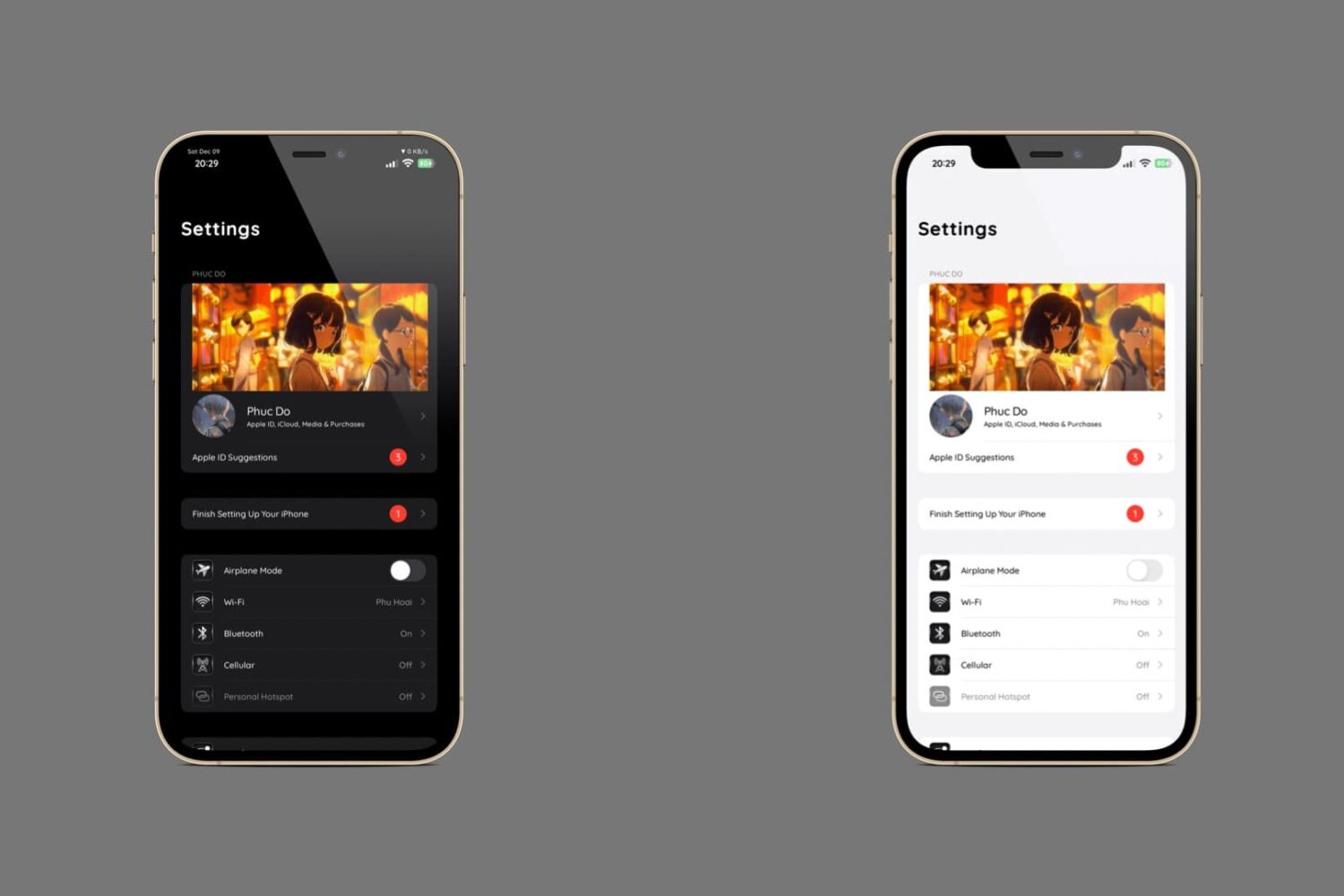
Those of you that take advantage of the Misaka package manager app to install hacks and add-ons on your MacDirtyCow or kernel file descriptor (kfd) exploit-vulnerable device might be interested to learn that there is now a new version of the project available to download.
Misaka v8.1.1 released with fix for issue where kfd exploit would stop working on iPad models