Most associate the term jailbreaking with devices like the iPhone, iPad, and in some cases, even the Apple TV. But when gifted hackers began experimenting with the powerful checkm8 hardware-based bootrom exploit earlier this year, things got more interesting. In March, for example, checkra1n team member Luca Todesco demonstrated nifty hacks on the OLED Touch Bar of a T2 chip-equipped MacBook Pro.
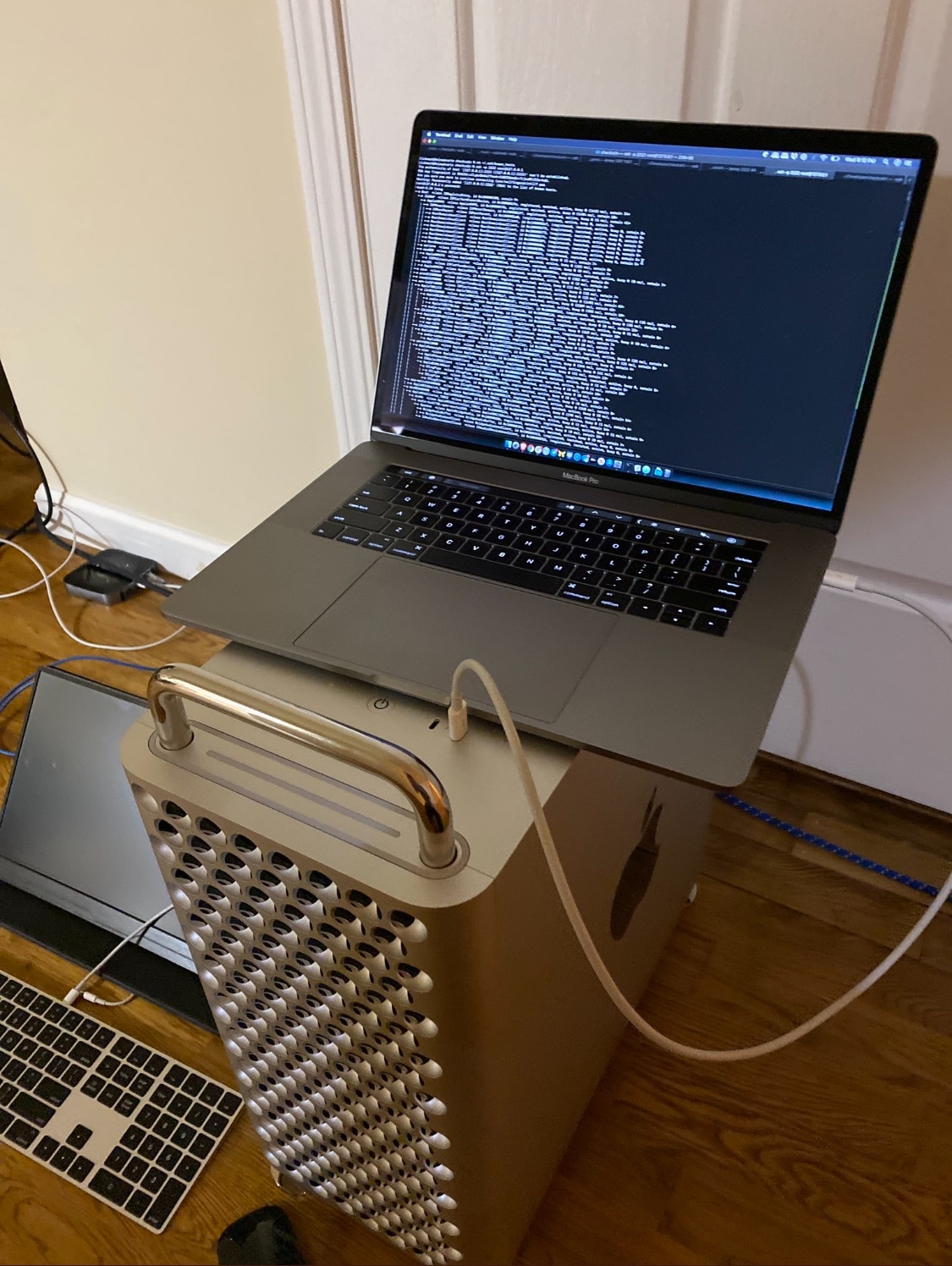
But the MacBook Pro isn’t the only Apple computer that sports a T2 chip. As a matter of fact, many do, and with that in mind, it may not come as much of a surprise that the checkra1n team has taken things a step further by jailbreaking yet another T2-equipped Mac – the elaborate and expensive Mac Pro:
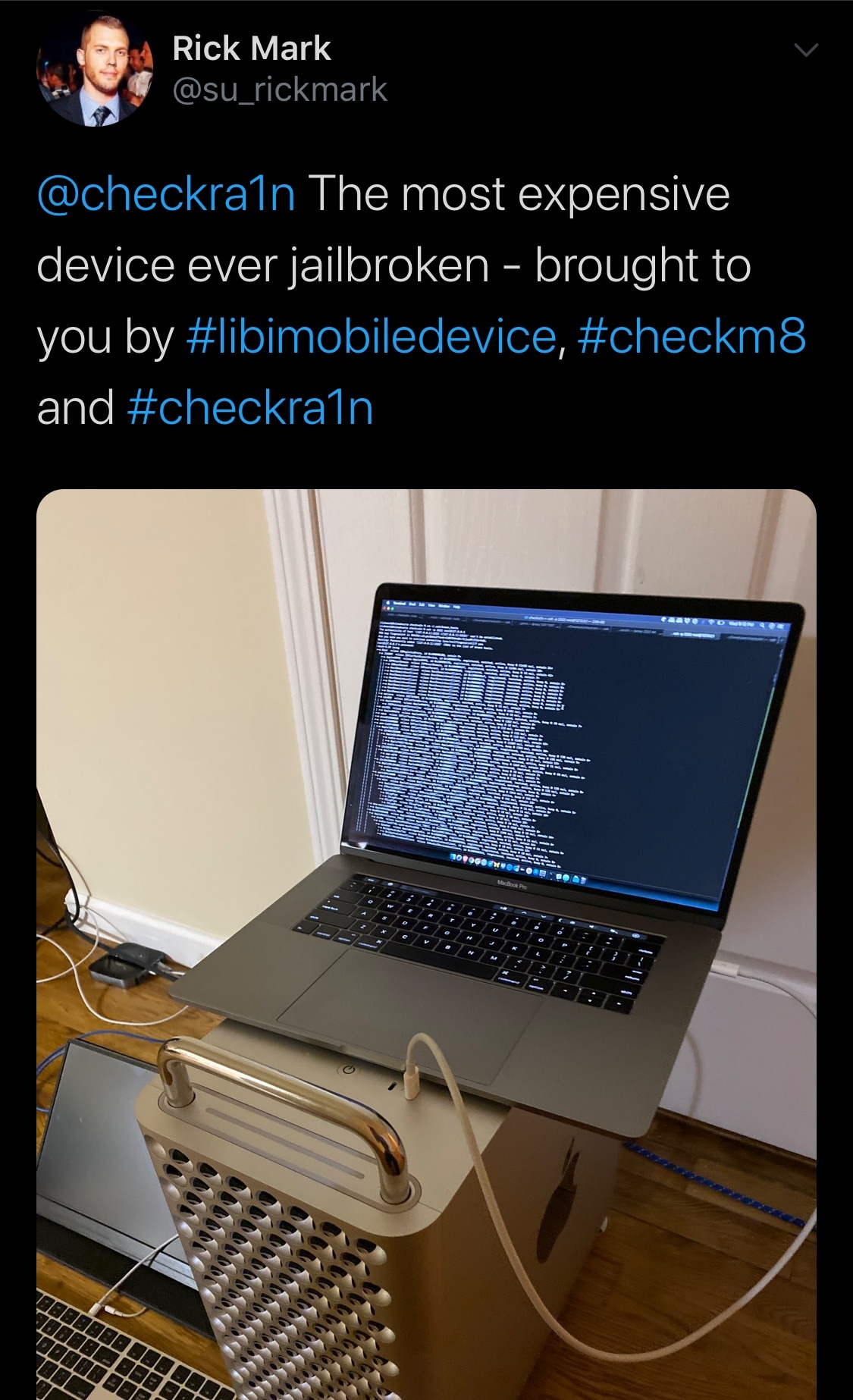
The captivating feat was shared first via Twitter by checkra1n team member Rick Mark Monday afternoon and later Retweeted by Luca Todesco. The Tweet contained an impact that appeared to depict Apple’s latest Mac Pro being given the checkm8 bootrom exploit treatment with the help of an accompanying MacBook Pro.
It’s worth noting that a Mac’s T2 chip manages its security in terms of the secure enclave, which involves Touch ID authentication, encrypted SSD storage, and secure boot-ups, among other things. Apple also says that a Mac’s T2 chip is responsible for managing its System Management Controller, image signal processor, and SSD controller on top of that.
It remains to be seen what types of benefits someone might gain from hacking their T2-equipped Mac, but given just how much of our lives are stored on our computers these days, it’s also worth mentioning that such hacks could potentially impose security implications. The crucial types of information that a Mac’s T2 chip handles only reaffirms this concern.
Moreover, the Mac Pro doesn’t even have a Touch Bar like the previously demonstrated MacBook Pro-centric hacks, so there’s potentially even fewer benefits in this particular case. Nevertheless, the feat earns the checkra1n team bragging rights, as this very well could be the most expensive device ever jailbroken, and that’s not to be taken lightly.
As of now, this doesn’t look like much else than just a proof of concept intended to demonstrate the capabilities of the powerful checkm8 exploit, and so we don’t expect to see any tools released to the general public anytime soon. Regardless, it’s still awesome to see what’s possible with just a single widely available hardware exploit that Apple can’t patch without releasing new hardware for future machines.
Are you excited to see what becomes of these T2-centric hacks? Let us know why or why not in the comments section below.