
If you’ve been following along with trends in the jailbreak community recently, then you’ve undoubtedly caught wind of hacker and security researcher Brandon Azad’s plans to release a tfp0 exploit proof-of-concept targeting the iPhone 11 on iOS 13.3.
The news, announced just yesterday, has good implications for jailbreaking. It means that jailbreaks could potentially be devised for devices running iOS 13.3, perhaps even other handsets of the A13 variety. But who will make them?
As it turns out, unc0ver lead developer Pwn20wnd is particularly interested in Azad’s upcoming exploit, and he took to Twitter early Wednesday morning to share that he would be working on updating the unc0ver jailbreak for iOS 13.0-13.3 following the release of the aforementioned exploit.
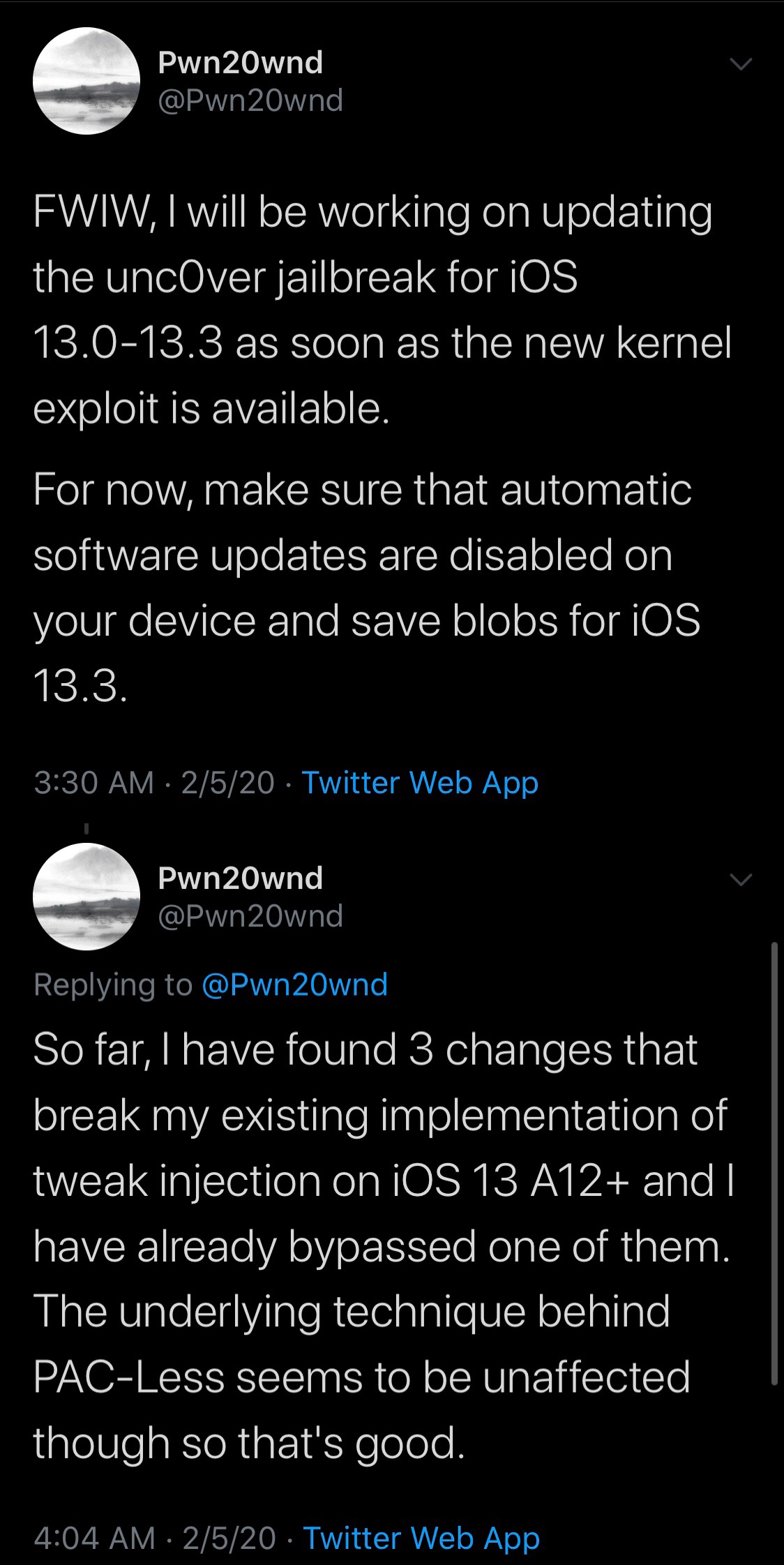
As a measure of preparation, Pwn20wnd advised that avid jailbreakers downgrade from iOS 13.3.1 to to iOS 13.3 immediately while it’s still being signed. Moreover, jailbreakers should save their iOS 13.3 blobs and turn off automatic software updates to prevent their iPhone from downloading and installing the latest (unjailbreakable) firmware.
In a follow-up Tweet, Pwn20wnd added that his implementation of tweak injection for A12(X) on iOS 13 — the means of loading and using jailbreak tweaks and extensions — is broken by three substantial changes. This is something that Pwn20wnd will need to fix if a full-fledged jailbreak is to be made by way of unc0ver on iOS 13.0-13.3. Otherwise, we might see something partial for the time being.
On /r/jailbreak, Pwn20wnd has said that there are no ETAs for his work at this time, so for now, we’ll just have to wait and see what happens.
The only official iOS 13 jailbreak at the time of this writing is checkra1n, which only supports up to the iPhone X due to hardware exploit limitations. Should unc0ver pick up this claimed support, it would be the first jailbreak to support Apple’s latest devices on iOS 13.
Are you excited to witness the fruits of Azad’s latest tfp0 exploit? Let us know in the comments section below.