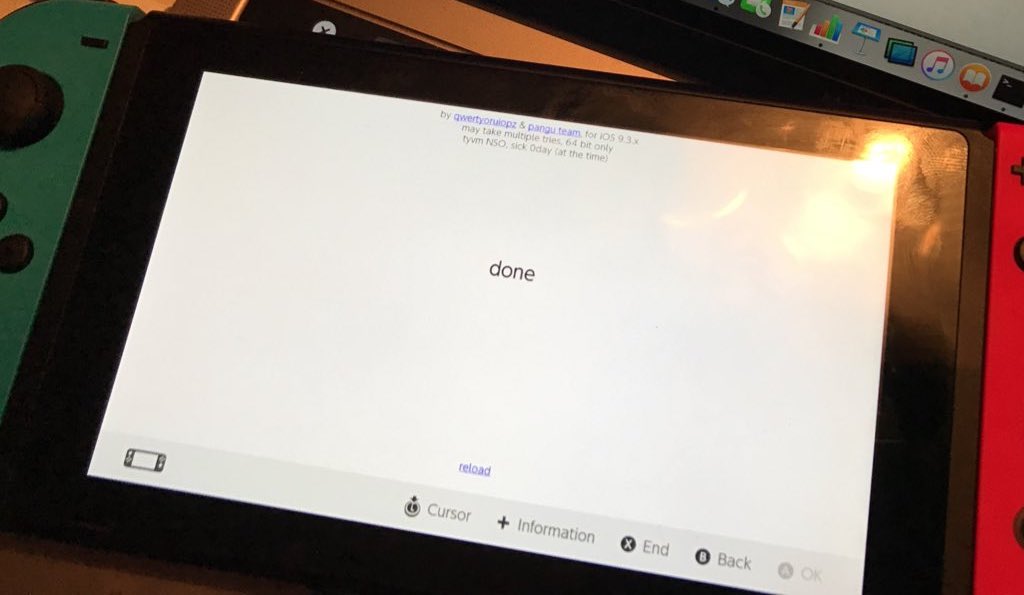
A little over a week after the release of Nintendo’s new console, the Switch, reputed iOS hacker Luca Todesco has posted an image of an adapted version of his WebKit exploit running on the device.
As explained in a detailed proof-of-concept created by LiveOverflow, It seems that the Switch shipped with a somewhat antiquated browser, one whose version of WebKit was still vulnerable to the same exploit utilised by Todesco’s browser-based jailbreak for iOS 9.3.x.
Our jailbreaking readers will likely remember Todesco’s tool, called JailbreakMe. It used the exploit known as CVE-2016-4657 to execute arbitrary code via the Safari browser and is hosted on Todesco’s website. This allows users of the Pangu jailbreak for iOS 9.2-9.3.3 to re-jailbreak their devices indefinitely, alleviating the certification issues which would otherwise have plagued them, and which have plagued the iOS 10 jailbreak.
The bug was patched in more recent versions of the open-source WebKit engine, and was likewise fixed up in iOS 9.3.5, but apparently the Nintendo Switch’s bundled browser is behind the times and still contains this critical vulnerability. Whether Nintendo had already assembled and flashed these devices before its discovery is not known for sure, but seems unlikely. Perhaps they just didn’t consider it a priority to update the Switch’s browser too religiously before release, given that it is not generally user-facing, and is only invoked when trying to connect to Wi-fi networks which require a captive portal.
Noticing the ongoing applicability of CVE-2016-4657 whilst playing around with the Switch, Todesco was able to adapt the tool by removing the iOS specific code, and gain code execution, solely within the browser. It should be noted however, that this does not constitute a full jailbreak by any means. It will however be of use in further investigating the inner workings of the device.
LiveOverflow’s POC details the changes that were made to the original JailbreakMe exploit in order for it to work, and he has also released an in-depth video which explains how it is deployed to the Switch. It involves using a laptop to simulate a captive portal in order to launch the Switch’s browser from within its Wi-fi settings. By setting up a proxy on the laptop, the captive portal can be made to redirect to a website of your choice, in this case, an adapted JailbreakMe exploit page.
For further details on the process, feel free to watch the full video below:
Whilst this news does not imply that the Switch is close to being fully jailbroken, it is a first step, and is certainly notable in its transference of the underlying bug. It seems slightly lax of Nintendo to have shipped a browser incorporating such a powerful and well-known exploit, but at this point it has only been used to gain code execution within the browser, not over the entire system. It has also been suggested that Nintendo can issue an update to patch the vulnerability that will not require user authentication, making it difficult to remain on an exploitable software version, though this remains to be confirmed.
Have you got your hands on a Switch already? Would you be interested in a jailbroken Switch, if such a thing did eventually come to pass? Let me know.