According to Bloomberg, which anonymously cited people close to law enforcement, malware which other victims described as “sophisticated,” was placed on the popular developer forum to potentially gain access to data stored on corporate computers…
Tuesday Apple confirmed the attack, but said there was “no evidence that any data left Apple.” The company said the attackers exploited a vulnerability in the Java plug-in for browsers and issued a patch three hours later.
Investigators now have tracked one server they think was used by criminals in Russia or Eastern Europe. That server was part of a hosting company in the Ukraine, according to Bloomberg.
The changing focus of the investigation departs from growing suspicion that Unit 61398, an elite cyberunit of China’s People’s Liberation Army, was behind the attack. Tuesday, the New York Times – itself a victim of hackers – reported that the nation’s military hackers were targeting Western corporations.
American intelligence officials exposed this 12-story building on the outskirts of Shanghai as the headquarters of Unit 61398 of the People’s Liberation Army.
Apple’s infection began when employees visited the popular iPhoneDevSDK forum, falling victim to a security hole in their browsers. That tactic is known as a “waterhole” attack, since victims behave like animals drawn to a waterhole, according to RSA Security.
In this case, the enticement was early access to software surrounding the iPhone which developers could use to prep their warez for upcoming Apple gear.
Security experts also said the malware was likely not targeting Apple itself, but developers working for other companies which would then infect their computers.
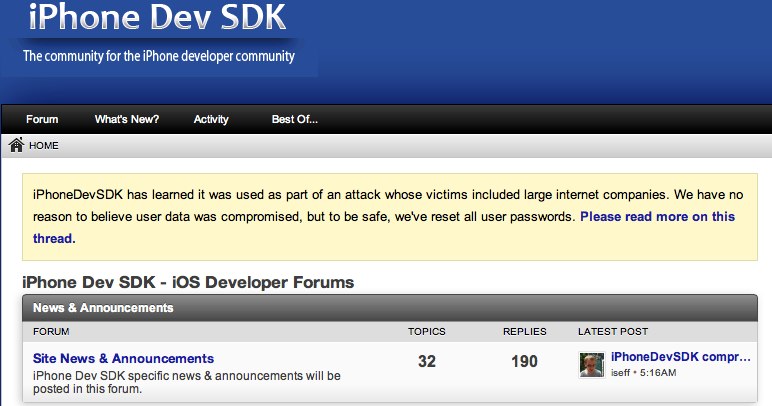
MacRumors highlighted today a blog post today from iPhoneDevSDK owner Ian Sefferman who shares details on how the hackers compromised his web site to launch attacks on Facebook and Google.
What we’ve learned is that it appears a single administrator account was compromised. The hackers used this account to modify our theme and inject JavaScript into our site. That JavaScript appears to have used a sophisticated, previously unknown exploit to hack into certain user’s computers.
We’re still trying to determine the exploit’s exact timeline and details, but it appears as though it was ended (by the hacker) on January 30, 2013.
As with Facebook, it’s important to stress that we have no reason to believe user data was compromised.
The social networking giant announced last Friday it was the victim of hackers, who infected a website used by mobile developers.
Twitter may have acted as the front door for this latest rash of hacking.
The service announced earlier this month that information on around 250,000 users may have been snagged via an attack.
The attack, which Twitter described as “very sophisticated,” may have provided hackers clues on how to launch subsequent assaults.
So far, Along with Apple, the New York Times, the Wall Street Journal, the Washington Post, Facebook and Twitter have acknowledged being hacked.