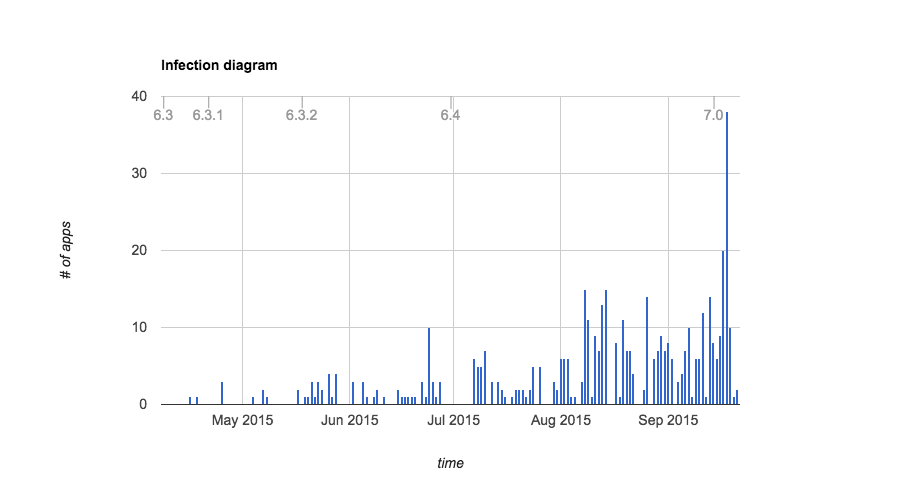
The XcodeGhost malware couldn’t have arrived at worst time for Apple as the company prepares to launch its iPhone 6s and iPhone 6s Plus tomorrow. The company has already removed the App Store apps infected by the malware, which has been found to inject its payload into apps compiled with compromised copies of Xcode that were distributed on non-Apple servers in China.
Wednesday, the Cupertino firm has confirmed plans to mitigate the threat by hosting local Xcode downloads within China. In addition, Apple has posted an XcodeGhost FAQ webpage on its Chinese website detailing the XcodeGhost malware and how customers might be affected by it.
“We’re working to make it faster for developers in China to download Xcode betas,” Apple said. Xcode is Apple’s tool required for iOS and OS X development.
Writing on the Chinese social media site Sina, Apple’s marketing boss Phil Schiller acknowledged that Chinese developers inadvertently downloaded hacked Xcode builds from local sources due to slow loading times from Apple’s servers.
“In the US it only needs 25 minutes to download,” Schiller told Sina.
In China, it “may take three times as long” to download the full multi-gigabyte Xcode build. Apple will be providing an official source for developers in the People’s Republic to download Xcode domestically, CNET reported.
Yesterday, the iPhone maker emailed developers instructions on using Terminal on OS X to check if their Xcode copy has been tampered with.
The harmful malware collects and sends information about infected devices. An analysis by Appthority has confirmed that XcodeGhost cannot display login prompts or request text from users in order to fool them into revealing their Apple ID credentials.
Here’s what the malware does, as per Appthority.
- Sends requests to the server (using a fixed timer interval between requests)
- The request contains all kinds of device identifiers (like a typical tracking framework)
- The response can trigger different actions:
- Shows an AppStore item within the app by using a SKStoreProductViewControllerDelegate
- Showing an UIAlertView and show the AppStore view depending on which button was tapped
- Open an URL
- Sleeping for a given time
So, while the malware cannot initiate iOS’s native Apple ID and iCloud logins, it can take users to a malicious webpage that imitates Apple’s web login prompts. If anything, the attack has managed to prove that the App Store can be compromised on a large scale.
Apple's Phil Schiller tells China's Sina website that Apple knows of no cases where malicious apps transmitted user data.
— CNBC Now (@CNBCnow) September 22, 2015
So, how can you tell if your iDevice has been compromised by the malware?
According to Apple, there’s no information to suggest that the malware has been used to do anything malicious or that this exploit would have delivered any personally identifiable information had it been used.
“We’re not aware of personally identifiable customer data being impacted and the code also did not have the ability to request customer credentials to gain iCloud and other service passwords,” reads the FAQ.
“As soon as we recognized these apps were using potentially malicious code we took them down,” it reads. “Developers are quickly updating their apps for users.”
“Malicious code could only have been able to deliver some general information such as the apps and general system information.”
So, is it safe then to download apps from App Store?
“We have removed the apps from the App Store that we know have been created with this counterfeit software and are blocking submissions of new apps that contain this malware from entering the App Store,” Apple writes.
The company is now working closely with developers to get impacted apps back on the App Store as quickly as possible.
“A list of the top 25 most popular apps impacted will be listed soon so users can easily verify if they have downloaded the latest versions of these apps,” the FAQ continues. “After the top 25 impacted apps, the number of impacted users drops significantly.”
Apple claims it will be informing customers if they’ve downloaded any app that might have been compromised. “Once a developer updates their app, that will fix the issue on the user’s device once they apply that update.”
MacRumors has put together an even richer XcodeGhost FAQ for those interested to learn more about this new type of threat targeting the iOS platform.