Stefan Esser, better known in the jailbreak community as i0n1c, was responsible for one of the most successful exploits in jailbreak history. While the iOS 4.3.1 jailbreak was certainly a collaborative effort, Esser’s work was perhaps the most important.
No one likes to connect their iDevice to their computer every time they reboot, and i0n1c’s untether meant they didn’t have to. What made it so successful? The fact that the exploit continued to work through iOS 4.3.2 and 4.3.3 updates.
Have you ever wondered what goes into hacking the most secure mobile operating system? Esser tells all in this 97 page paper…
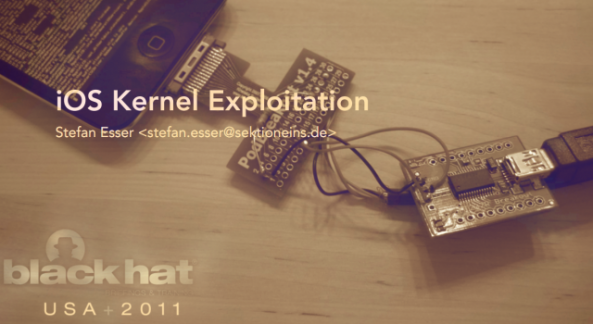
Stefan Esser was a speaker at the annual Black Hat Security Conference, held in Las Vegas last month. He gave a presentation based on a paper he wrote entitled iOS Kernel Exploitation. iPhoneinCanada provides an excerpt from his speech:
“The iPhone user land is locked down very tightly by kernel level protections. Therefore any sophisticated attack has to include a kernel exploit in order to completely compromise the device. Because of this our previous session titled “Targeting the iOS Kernel” already discussed how to reverse the iOS kernel in order to find kernel security vulnerabilities. Exploitation of iOS kernel vulnerabilities has not been discussed yet.”
During his presentation, i0n1c also revealed the hardware he used to hack iOS. Among the tools were a 470k resistor, a USB to Serial breakout board, a PodGizmo connector, and two mini USB-B to USB-A cables.
This stuff goes way over our heads. But if you’re interested in reading i0n1c’s full paper, you can read all 97 pages of it here. It’s amazing that all of this work can be replicated by jailbreakers with the click of a button.
What do you think? Anyone planning on trying it out? (We’re probably just going to stick with RedSn0w — much simpler that way.)
