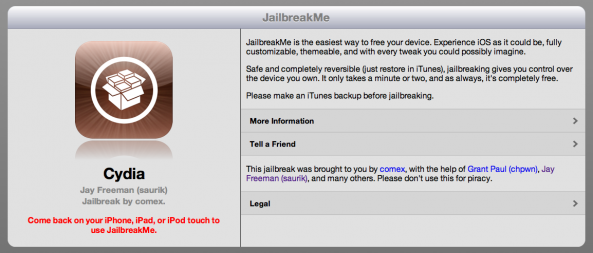
If you may recall, with the release of the long awaited JailbreakMe 3.0 for iOS 4.3.3, literally 10 days later Apple patched the clever PDF exploit in iOS 4.3.4. The security exploit could be triggered by viewing a maliciously crafted PDF file which may lead to an unexpected application termination or arbitrary code execution.
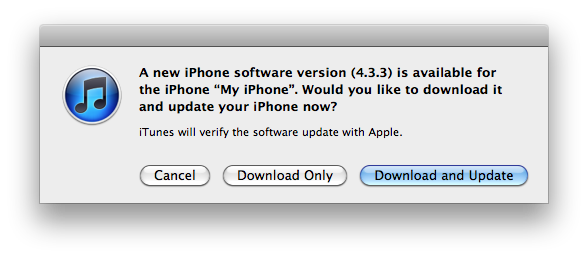
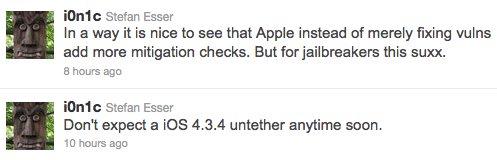
While the main reason Apple patched the exploit was to stop the use of JailbreakMe, it can also be a security concern. A few days later, Apple released another iOS software update, iOS 4.3.5. Apple released this update to patch the certificate validation vulnerability.
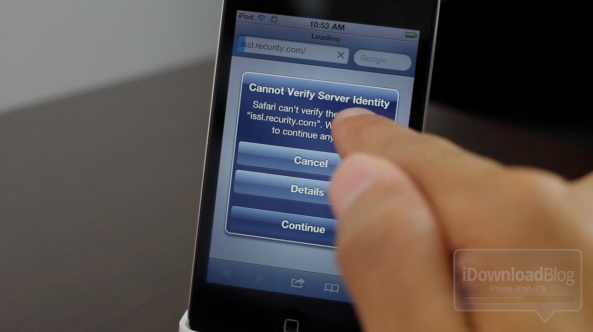
If you love customizing your iDevice to the fullest, you've probably already jailbroken, unless you didn't update by accident or purchase your iDevice after Apple stopped signing iOS 4.3.3. Unfortunately, while not updating to the latest software may preserve your jailbreak, you may also be at risk from the same vulnerability...