Several key vulnerabilities that have been discovered recently in the Wi-Fi standard put just about every router, smartphone and computer out there at risk of having users' personal information intercepted, exposed and stolen.
Encryption
macOS High Sierra 10.13 Supplemental Update fixes Keychain & APFS Disk Utility vulnerabilities

Apple on Thursday released a supplemental update to macOS High Sierra 10.13 which fixes a few bugs, among them a major vulnerability (we told you about it this morning) that could expose the passwords of encrypted Apple File System volumes in plain text in Disk Utility.
macOS High Sierra’s Disk Utility exposes passwords of encrypted APFS volumes
Brazilian developer Matheus Mariano has discovered a pretty serious security vulnerability in macOS High Sierra which exposes passwords of any encrypted APFS volumes in plain text.
Apple won’t release a fix for Secure Enclave’s exposed decryption key

Following the exposure of the decryption key protecting the firmware software running on the iPhone 5s's Secure Enclave coprocessor that was posted on GitHub yesterday, an Apple source has reportedly said that any customer data securely stored in the cryptography coprocessor remains protected and that the company does not intend to roll out a fix at this time.
Decryption key for iPhone 5s’s Touch ID Secure Enclave coprocessor has been exposed

Ahead of this year’s Hack in the Box (HITB) conference in Singapore, security researcher who goes by the Twitter handle “xerub” has managed to expose the fully grown decryption key for the iPhone 5s's cryptographic coprocessor that handles Touch ID, called Secure Enclave.
AI powered, end-to-end encrypted calls now available in Telegram Desktop
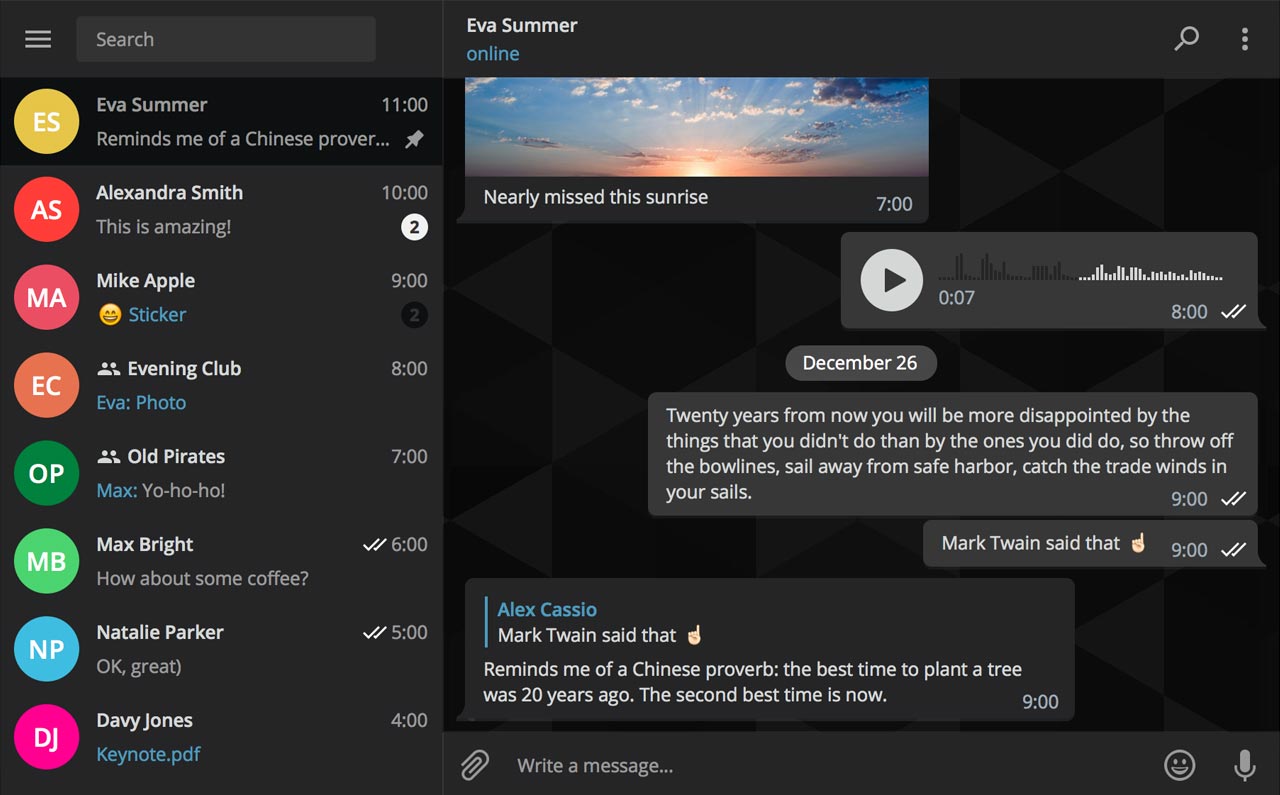
Secure instant messaging service Telegram today launched voice calls in its desktop app for Mac, Windows and Linux nearly two months after implementing the voice-calling feature in Telegram Messenger for iPhone and iPad.
To make sure Telegram calls are the best in terms of quality, speed and security, the app uses artificial intelligence to update its neural network after each call about things such as network speed, ping times, packet loss percentage and other factors that influence the quality of your VoIP calls.
Based on gathered data, the app optimizes dozens of parameters to improve the quality of future calls on the given device and network. By default, Telegram calls are lightweight.
https://twitter.com/telegram/status/864543129847955457
If there's a change in your connection during the call, the app will make necessary adjustments.
For instance, Telegram may boost your sound quality on stable Wi-Fi connection or use less data if your Wi-Fi or cellular coverage is spotty at best.
Whenever possible, your calls will go over a peer-to-peer connection using the best audio codecs to save traffic while providing “crystal-clear quality.” When a peer-to-peer connection cannot be established, the app will use the closest server to you.
Telegram has its own distributed infrastructure all over the world to ensure the fastest possible delivery of your texts and seamless voice calling experience. As mentioned, VoIP calls on Telegram use end-to-end encryption, just like the app's Secret Chats feature, to prevent eavesdropping.
For voice calls, however, they've improved the key exchange mechanism. “To make sure your call is 100 percent secure, you and your recipient just need to compare four emoji”, said the team.
Bottom line: the quality of Telegram calls will further improve as you and others use them, thanks to the built-in machine learning. And with group calling, video calling and screen sharing apparently on the team's to-do list, Telegram is bound to become a capable Skype alternative.
As soon as VoIP calls are enabled for your country, a phone icon will appear on every profile page in Telegram Desktop.
Telegram for iOS is available free via App Store.
Telegram Desktop can be downloaded from Mac App Store or through the official website.
WhatsApp quietly added encryption to iCloud backups in late 2016

WhatsApp last year closed an important security loophole by adding encryption to users' chat backups stored in iCloud. Before the change, hackers could theoretically gain access to WhatsApp chat archives in iCloud using third-party forensic tools to access underlying messages in a readable form.
Rather than rely on iCloud Drive to protect customer data, the Facebook-owned company has added a unique encryption key created by the WhatsApp app.
A spokesperson confirmed iCloud backups are now being encrypted, telling Forbes: “When a user backs up their chats through WhatsApp to iCloud, the backup files are sent encrypted.”
Although Apple holds the encryption keys for iCloud, it's up to app makers to use encryption when sending user data to iCloud. According to TechCrunch, a Russian company called Oxygen Forensics, which supplies mobile and cloud hacking tools, was able to generate encryption keys for WhatsApp's iCloud backups.
The workaround requires that an attacker have access to a SIM card with the same mobile number that the app uses to send a verification code to generate the encryption key for the iCloud backup. Of course, Oxygen still needs a user's Apple ID and password to gain access to their iCloud user space in the first place.
“Then, using the associated SIM, Oxygen said it can generate the encryption key for decrypting the data by passing the verification process again,” explains TechCrunch. Forbes suggests the method could be used by police in possession of a device where the WhatsApp account has been deleted but iCloud backups have not been wiped.
https://twitter.com/FiloSottile/status/861569977681412096
In other words, after realizing that forensic tools could be used to download encrypted WhatsApp data from iCloud backups in a readable form, WhatsApp has beefed up security and quietly rolled out encryption for iCloud backups last year.
You can backup your entire WhatsApp chat archive to iCloud by tapping the Settings tab in the lower-right corner of the app. Now tap Chats, then Chat Backup and finally hit Back Up Now.
By the way, WhatsApp should update the wording of the Chat Backup screen because it states, somewhat confusingly, that “media and message you back up are not protected by WhatsApp end-to-end encryption while in iCloud.”
Viber rolls out self destructing Secret Chats
Messaging service Viber today rolled out a new Secret Chats feature. Not to be confused with Secret Messages, a similar feature introduced in February 2017 that lets you define how long your photos, videos and texts are available after the recipient has opened them, Secret Chats use Viber's end-to-end encryption let you set a timer on individual messages so they disappear after a few seconds, get an alert when a screenshot is taken and be sure no messages get forwarded.
WhatsApp has a backdoor that allows snooping on end-to-end encrypted messages [updated]
In 2016, WhatsApp finally enabled complete end-to-end encryption for both chats and video calls to ensure that no one but the intended recipient can decipher contents of their communications. Unfortunately, it's come to light that WhatsApp's system has been plagued by a major vulnerability which was discovered by Tobias Boelter, a cryptography and security researcher at the University of California, Berkeley.
In an interview with the British newspaper The Guardian, Boelter said the backdoor could let Facebook read end-to-end encrypted content, meaning the social network could be complied with court orders to make decrypted messages available to law enforcement and other government agencies
UPDATE: We've received a response from WhatsApp regarding the alleged backdoor.
Here’s everything Cellebrite’s forensic tool can extract from iPhones
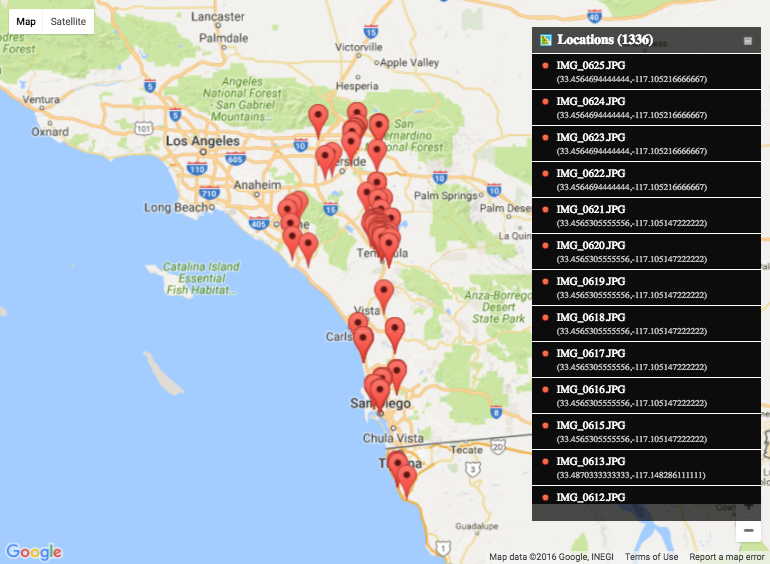
Documents uncovered by ZDNet have revealed the true scope of technology from Israeli developer Cellebrite Mobile Synchronization, which specializes in smartphone data extraction, transfer and analysis.
The leaked documents show just how much private data its smartphone forensic tool UFED, used by law enforcement, is capable of extracting from iPhones.
In a single data-extraction session, investigators were able to collect a huge array of personal data from an iPhone 5 like messages, phone calls, voicemails, images and more, including some deleted content. UFED can pull similar data from other phones, too, including Wi-Fi hotspots and cellular towers the device's was connected to.
macOS Sierra 10.12.2 fixed vulnerability that let attackers obtain disk encryption password

Last week's macOS Sierra 10.12.2 software update squashed a number of bugs and patched a few newly discovered vulnerabilities, among them one that allowed an attacker to obtain your FileVault disk encryption password by plugging in a $300 Thunderbolt device into a locked or sleeping Mac.
As detailed by security researcher Ulf Frisk, attackers must have physical access to your Mac in order to exploit the vulnerability. The obtained password may be used to unlock your Mac's disk and access everything on it.
WhatsApp rolls out end-to-end encrypted video calling

Facebook-owned WhatsApp announced yesterday that it had begun rolling out video calling to the more than one billion users it claims across iOS, Android and Windows Phone platforms around the world.
According to TechCrunch, video calls on WhatsApp are end-to-end encrypted just like with FaceTime in order to prevent rogue parties from eavesdropping on your communications.
WhatsApp previously rolled out end-to-end encryption for chats. “We obviously try to be in tune with what our users want,” WhatsApp co-founder Jan Koum told Reuters. “We're obsessed with making sure that voice and video work well even on low-end phones.”