It’s never a dull moment for the jailbreak community, and this week, the spotlight isn’t so much on jailbreak tool releases as it is on a series of baseless DMCA (Digital Millennium Copyright Act) take-downs that appear to be targeting jailbreak-oriented software and iOS security research.
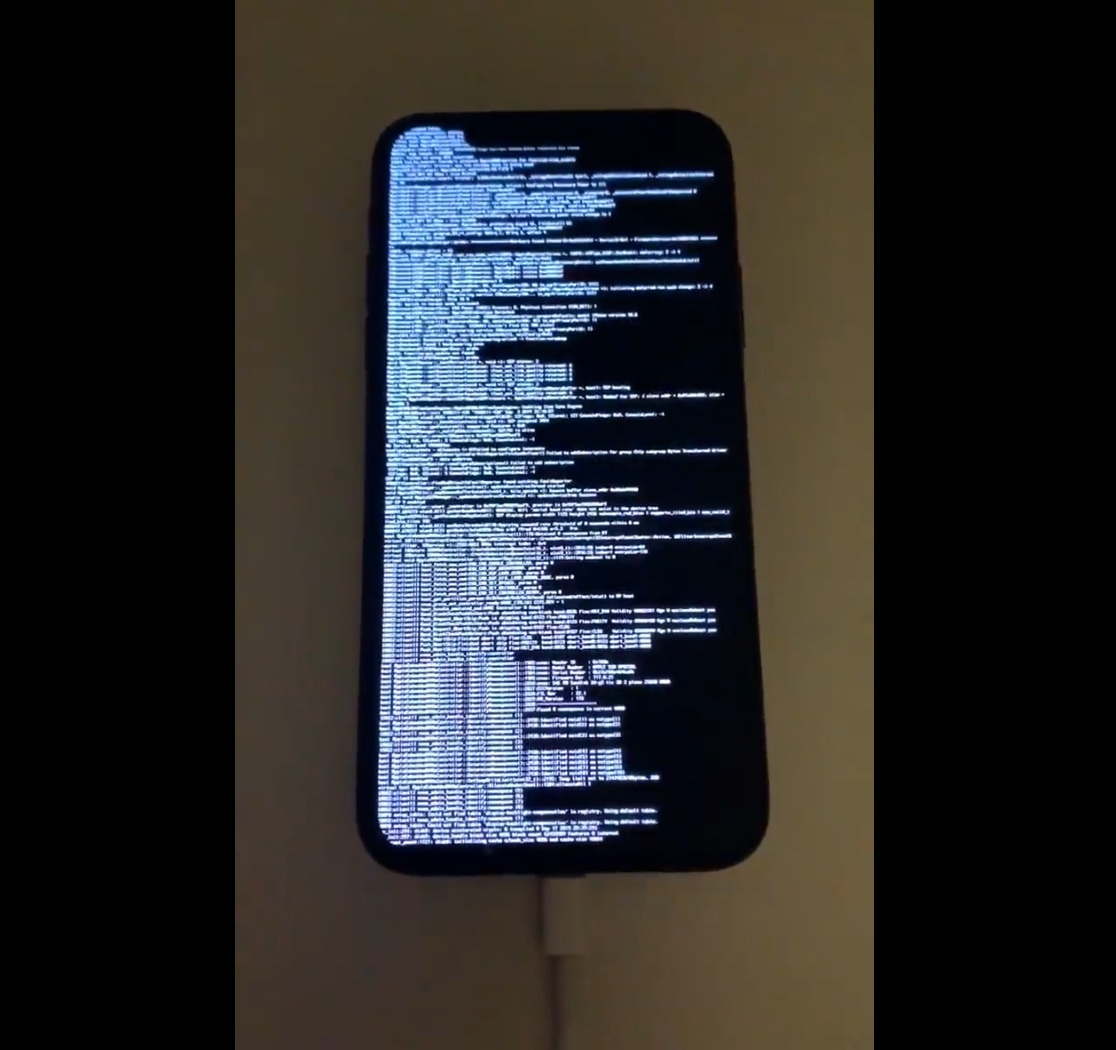
All the hubbub began with a simple Tweet shared by respected community hacker @siguza, which contained an iPhone encryption key. This key was comprised of a long string of randomized letters and numbers and would have appeared as gibberish to most common folk. Shortly after the Tweet fell victim to one of these requests, threads on the popular /r/jailbreak subreddit regarding checkra1n and unc0ver became victimized by similar activity: