In June of this year, Edward Snowden shocked the world by leaking a number of slides and documents and revealing that the NSA has backdoor access to the databases of 9 major tech companies, including Apple and Facebook. But as it turns out, its access may not be limited to software.
Since Snowden’s initial outing, there has been a number of subsequent reports and leaks. And the latest to garner gasps from the security community is that the NSA has the ability to intercept the delivery of a new computer or mobile device—including iPhones—and build in a remote backdoor…
Here’s the report from The Daily Dot:
“The U.S. National Security Agency has the ability to snoop on nearly every communication sent from an Apple iPhone, according to leaked documents shared by security researcher Jacob Appelbaum and German news magazine Der Spiegel.
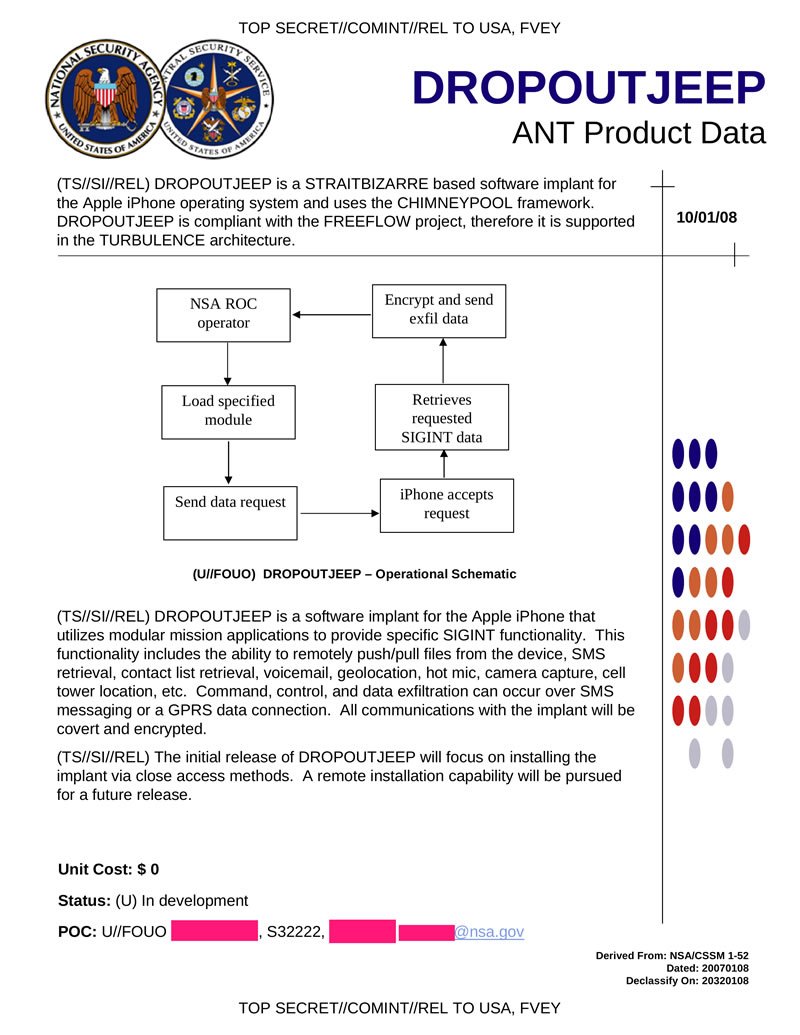
An NSA program called DROPOUTJEEP allows the agency to intercept SMS messages, access contact lists, locate a phone using cell tower data, and even activate the device’s microphone and camera.”
And here’s the document showing how DROPOUTJEEP works:
And finally, here’s a video of a lecture on the research:
http://www.youtube.com/watch?v=b0w36GAyZIA
According to the leaked documents, the NSA claims a 100% success rate when it comes to installing spyware on iOS devices. For now, it does require physical access to the device for proper installation, but the scary part is, it’s reportedly able to reroute shipments of devices ordered online to get it.
The general consensus is that this is all made possible by one of two scenarios: either the NSA has a huge collection of exploits that work against Apple products, and they are withholding critical information about the company’s systems. Or, perhaps the more worrisome, Apple sabotaged it themselves.
Apple has emphatically denied reports that it’s involved in the NSA PRISM program, and it has joined other tech companies in pushing for greater transparency from the US government and its subsequent agencies on court-ordered user information requests.
So, what do you make of all of this?