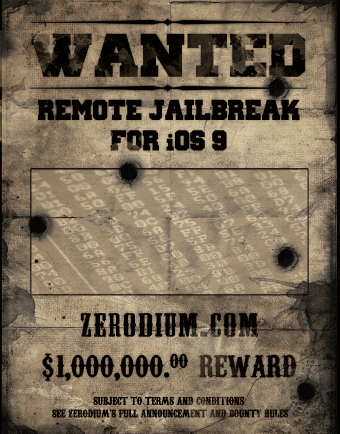
Vulnerability and exploit acquisition platform Zerodium announced today that the million dollar bounty it had put together has expired, noting that a team of researchers has won the prize. Launched in September of this year, the bounty program aimed at rewarding anyone one who would come forward with an “exclusive, browser-based, and untethered jailbreak for the latest Apple iOS 9 operating system and devices.”
It looks like they have their winners, as a team who made a remote browser-based iOS 9.1 and iOS 9.2 beta untethered jailbreak has apparently come forward. But don’t get your hopes too high.
Our iOS #0day bounty has expired & we have one winning team who made a remote browser-based iOS 9.1/9.2b #jailbreak (untethered). Congrats!
— Zerodium (@Zerodium) November 2, 2015
Zerodium is a company that acquires zero day exploits from security researchers in order to sell them to high paying customers, those customers usually being corporations or governments. Even if the news is indeed true, that exploit will not make its way to a jailbreak that could be available for people like you and me. If anything, this could be used by government agencies to hack into targets’ iPhones in order to retrieve information.
In essence, this is a one million dollar jailbreak you can’t have! I must say I am a bit skeptical about all this, but maybe I’m just too cynical. It is very unlikely Zerodium will disclose additional details about this, so we’ll just have to take their word for it.
Thanks PJ for the tip!