We often praise iOS as a very secure platform, and this is mostly true, as many studies have confirmed over the years. But sometimes, it’s not so much the platform that is responsible for the lack of security, it is the user himself.
The perfect illustration of this is when you jailbreak your device. By gaining root access to your iPhone or iPad, you start walking outside of Apple’s walled garden and actually put yourself at risk of having untrusted files installed on your device without your knowledge.
As a jailbreaker myself, I am very well aware of the risks, but I do not mind them because the benefits usually far outweigh the drawbacks, and I assume most jailbreak users feel the same.
This being said, a new malware called Unflod has been targeting jailbroken devices for a few weeks. While there is still a lot we don’t know about Unflod, the little information we have about it is enough to raise concerns…
The first mention of Unflod appeared on Reddit yesterday. After having many of his apps crash on his iPhone, Reddit user tdvx started disabling MobileSubstrate extensions and re-enabling them until he was able to single out a potential culprit: Unflod.dylib.
What is Unflod?
After looking a little more into it, Reddit user minilover11 found some troubling evidence that Unflod carries all the signs of a malware, capturing your Apple ID and password and sending them somewhere in China. He explains:
After using both Hopper and IDA (although I am by no means very good at reading assembly or intermediate code), Unflod.dylib seems overrides the function “SSLWrite” and captures appleId and password and their data from the raw plist data in SSL connections to Apple’s authentication server (/WebObjects/MZFinance.woa/wa/authenticate) and sends them to 23.88.10.4 (a Chinese site it seems, from the error message it displays, not bashing china or anything, just based off the text the website returns).
German security consulting firm SektionEins took to its blog and shared more findings about Unflod.
This malware appears to have Chinese origin and comes as a library called Unflod.dylib that hooks into all running processes of jailbroken iDevices and listens to outgoing SSL connections. From these connections it tries to steal the device’s Apple-ID and corresponding password and sends them in plaintext to servers with IP addresses in control of US hosting companies for apparently Chinese customers.
Although the source of the malware hasn’t been traced yet, it seems to be correlated to the installation of what I like to call “shady” repos (ie. pirate repos). So if you’ve installed some of these repos that distribute pirated tweaks, you could have been infected (cough cough).
How to know if you’ve been affected by Unflod
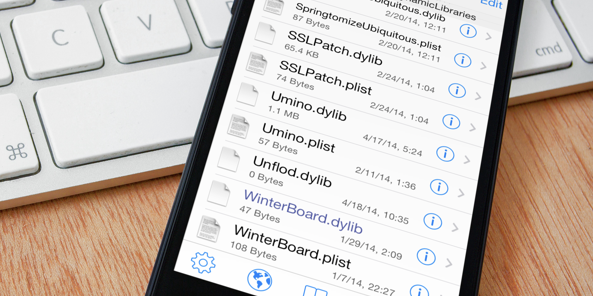
The best way to find out if you’ve been affected is to use iFile and navigate to /Library/MobileSubstrate/DynamicLibraries/. If you see a file named Unflod.dylib, then you are carrying this malware on your device.
How to remove Unflod
The quick and easy way to remove Unflod is to navigate to /Library/MobileSubstrate/DynamicLibraries/Unflod.dylib and delete the file. But as the folks at SektionEins note, deleting the Unflod dynamic library might not be enough as we’re not sure yet if more malware files were installed.
At the end of the day, the best thing to do to make sure you remove all potentially harmful files from your device is to restore in iTunes, which would ultimately lead to the loss of your jailbreak.
Change your Apple ID password now
If you have been affected, you should definitely follow the steps above to delete Unflod and then make sure to change your Apple ID password, which might have been compromised. Setting up two-step verification might be a good idea too.
Help figure out what Unflod is
Cydia Community Manager Britta has posted detailed instructions about how you can help Saurik figure out what Unflod is, where it’s from, etc… Find these instructions here.
More information
For more information, you may refer to the following posts:
- Original post on Reddit
- Follow up post on Reddit
- Instructions to help Saurik figure out Unflod
- Unflod analysis by SektionEins
Have you been affected by Unflod? As always, please make sure to share your findings here in the comments section.