Apple tonight broke its silence regarding Masque Attack, a recently discovered vulnerability in iOS. In a statement to iMore, the company says it encourages customers to only download apps from trusted sources and that it’s not currently aware of any users affected by the exploit.
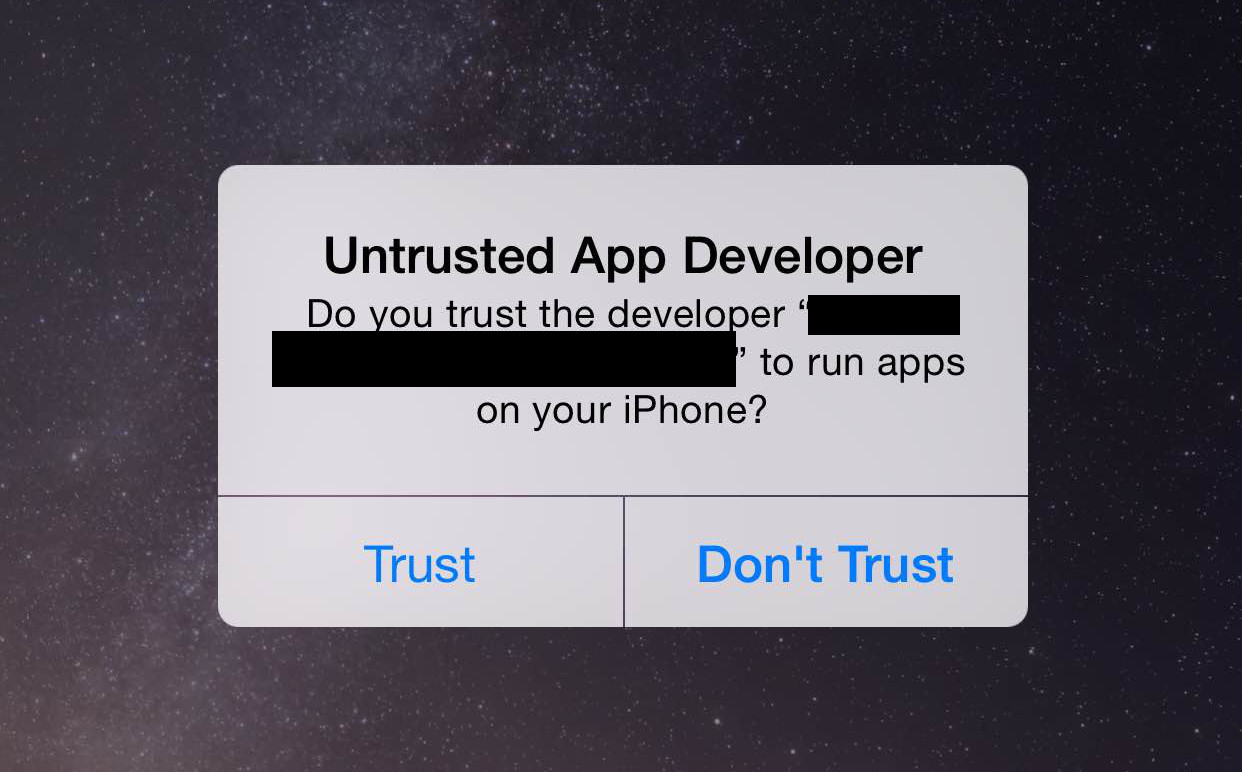
Research security FireEye announced its discovery of Masque Attack on Monday. The malware installs itself through a phishing link disguised as a new app or game, and then masquerades as a legitimate app. Once installed, it can access login credentials, credit card info and more.
Here’s Apple’s full statement:
“We designed OS X and iOS with built-in security safeguards to help protect customers and warn them before installing potentially malicious software,” an Apple spokesperson told iMore. “We’re not aware of any customers that have actually been affected by this attack. We encourage customers to only download from trusted sources like the App Store and to pay attention to any warnings as they download apps. Enterprise users installing custom apps should install apps from their company’s secure website.”
Apple’s comment comes just a few hours after United States government issued a warning to iOS users regarding Masque Attack. Earlier today, the National Cybersecurity and Communications Integration Center issued a bulletin describing the vulnerability and how it can be avoided.
Thanks to its oft-criticized “walled garden” approach to application installs, iOS has earned a reputation for being fairly secure. Masque Attack, however, takes advantage of a provisioning flaw in the operating system, which we are expecting to be patched in the upcoming iOS 8.1.1 release.
[iMore]