Skype users may soon be able to share their iPhone's screen during video calls.
Skype is testing the ability to share your iPhone’s screen during video calls
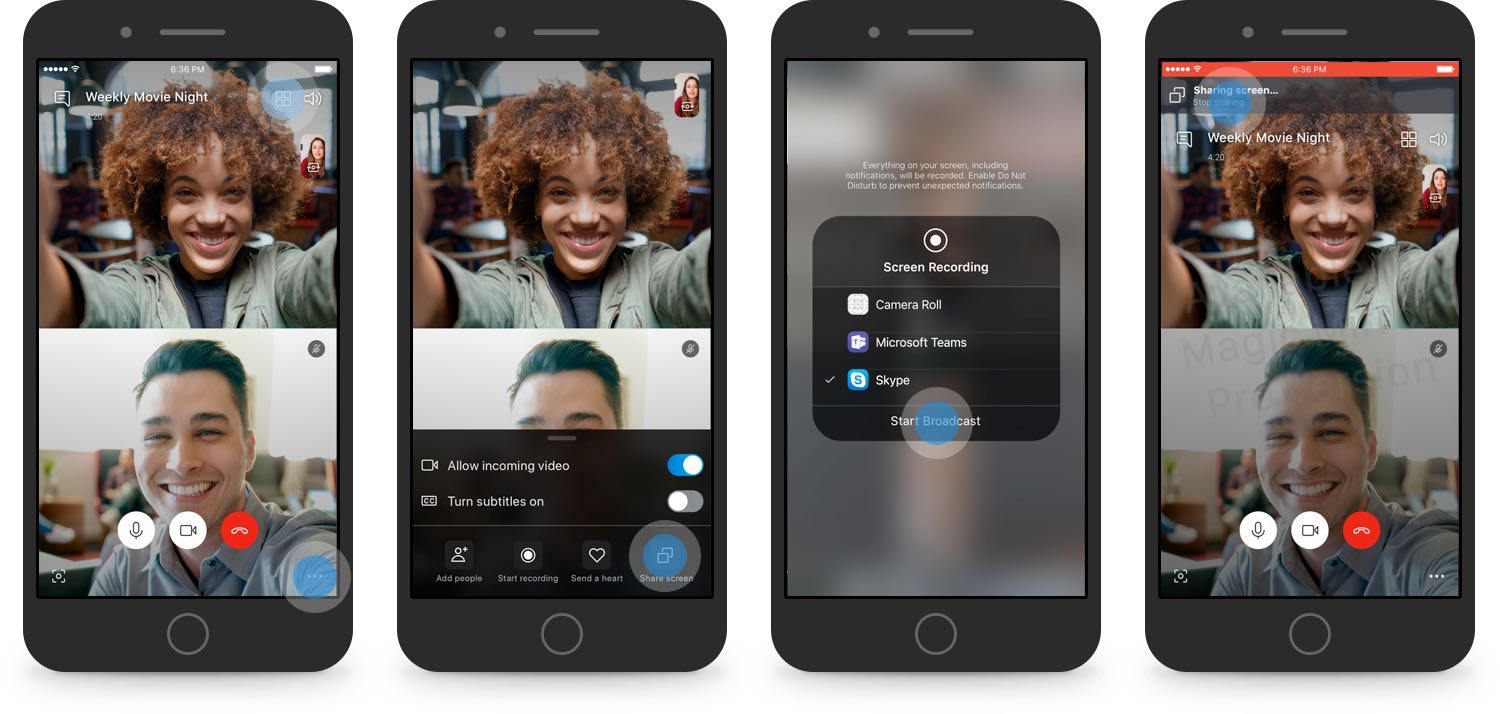
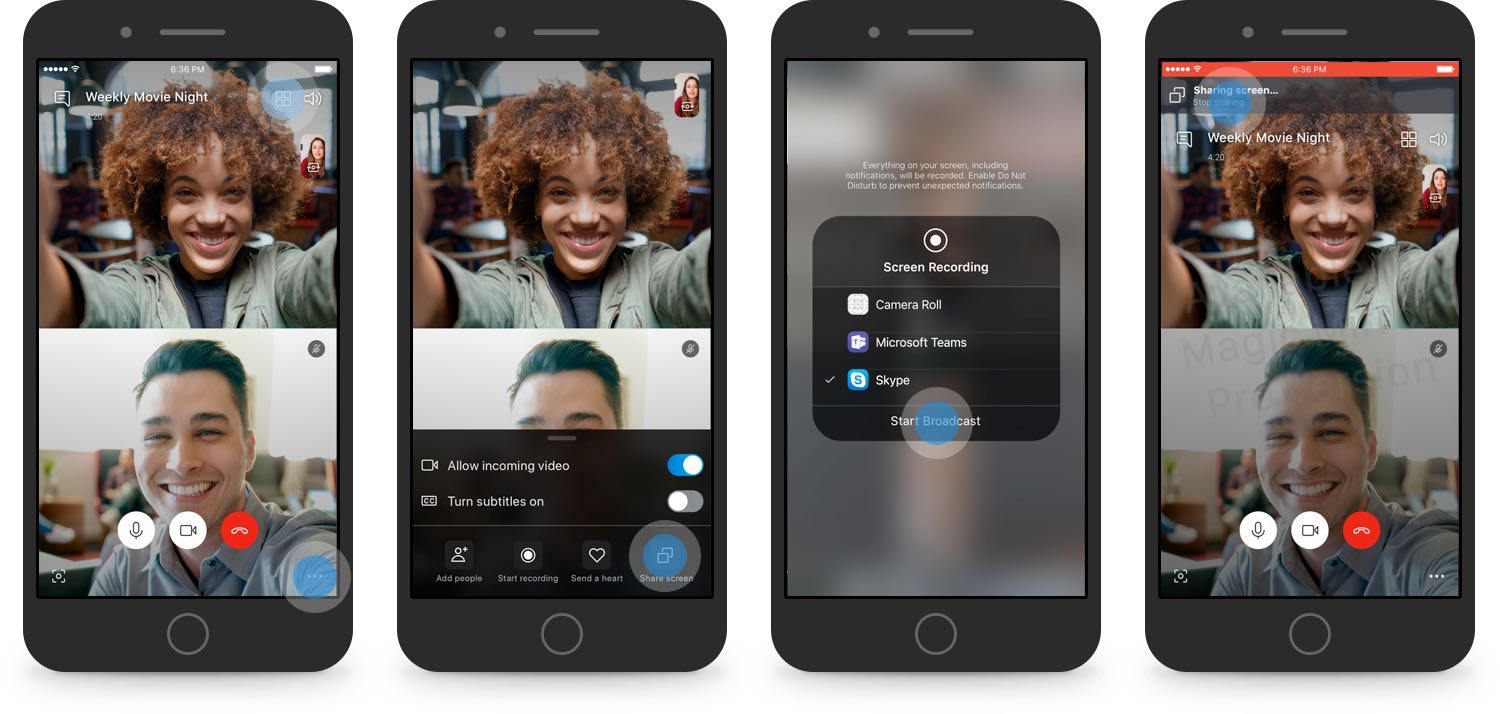
Skype users may soon be able to share their iPhone's screen during video calls.

Apple on Tuesday released the second betas of iOS 12.3, tvOS 12.3 and macOS 10.14.5 to the public. Those who are registered with Apple's public testing program can install the new software via each platform's respective OTA mechanism.

Apple today released second betas for the upcoming iOS 12.3, tvOS 12.3, macOS Mojave 10.14.5 and watchOS 5.2.1 software updates, arriving less than two weeks after the first betas were made available to the company's registered developers and public beta testers.

The Sileo Team on Friday pushed another update to the Sileo beta preview, bringing the pre-release package manager and Cydia alternative’s version number up to 0.8b8 from the previous version 0.8b4.
A Tweet shared by the Sileo Team just this morning describes what’s new in the update:

Hacker and unc0ver lead developer Pwn20wnd first introduced ‘partial’ A12(X) device support for the unc0ver iOS 12 jailbreak tool just under three weeks ago, but as most of the jailbreak community already knows, full support for A12(X) devices won’t be possible until Saurik first updates Cydia Substrate with compatibility for arm64e devices.
In a short spiel Monday afternoon, Pwn20wnd took to Twitter with a small status update for those still wondering about the status of the A12(X) jailbreak:

Apple on Thursday released the first betas of iOS 12.3 and tvOS 12.3 to public testers. The betas include the new TV app Apple unveiled on Monday, and registered testers can install the software via each platform's respective OTA mechanism.

Just two days after rolling out iOS 12.2 and other updates to consumers, Apple has begun a new beta cycle. On Wednesday, the company pushed out first betas of iOS 12.3 and tvOS 12.3 to developers. Registered devs can install the software via each platform's respective OTA update mechanism.

Apple on Monday seeded the sixth betas of iOS 12.2, tvOS 12.2, watchOS 5.2 and macOS 10.14.4 to developers. Registered devs can install the updates via each platform's respective OTA mechanism, or through the Developer Center. Today's releases come one week after beta 5, and one week before Apple's 'It's show time' media event, suggesting we are nearing the public launch.

It was only two weeks ago that security research @iBSparkes shared an iOS 11.0-12.1.2 exploit dubbed machswap with the general public, and just a few days later, hacker and unc0ver lead developer Pwn20wnd integrated the new exploit into his unc0ver jailbreak tool for A7-A9(X) devices running iOS 11.0-12.1.2. Fortunately, the fun isn’t stopping there.
As it would seem, @iBSparkes has been working on a newer exploit dubbed machswap2, which works in similar ways and supports A7-A12(X) devices running iOS 11.0-12.1.2. Perhaps more importantly, Pwn20wnd got it working with unc0ver, which means the jailbreak tool will soon support both the machswap or machswap2 exploits:

On Wednesday, hacker and unc0ver lead developer Pwn20wnd pushed a new revision to the unc0ver v3.0.0 pre-release, bringing it up to beta version 46.
Pwn20wnd shared news of the update via Twitter, adding that the update would fix significant instabilities on iOS 12 and make the system run noticeably faster:

Twitter this morning announced a brand new app that lets anyone become a beta tester for unreleased new Twitter features on iPhone and iPad.
Shortly after releasing an update for the unc0ver v3.0.0 pre-release with ‘partial’ support for A12 and A12X devices, Pwn20wnd dropped yet another revision, bringing the tool up to beta number 45 for public testing.
In a Tweet shared just this afternoon, Pwn20wnd reveals that the somewhat minor update addresses an issue involving the voucher_swap exploit by Brandon Azad on certain beta-centric firmware versions on A12(X) devices: