Apple on Wednesday issued a critical patch for macOS High Sierra to fix a major vulnerability discovered yesterday which allowed unrestricted access with full administrative privileges on Macs with a Guest account enabled or the root account’s password left blank.
The Security Update 2017-001 addresses a major bug in Directory Utility which allowed an attacker to bypass administrator authentication without supplying the administrator’s password. “A logic error existed in the validation of credentials,” says Apple.
The problem was addressed through improved credential validation.
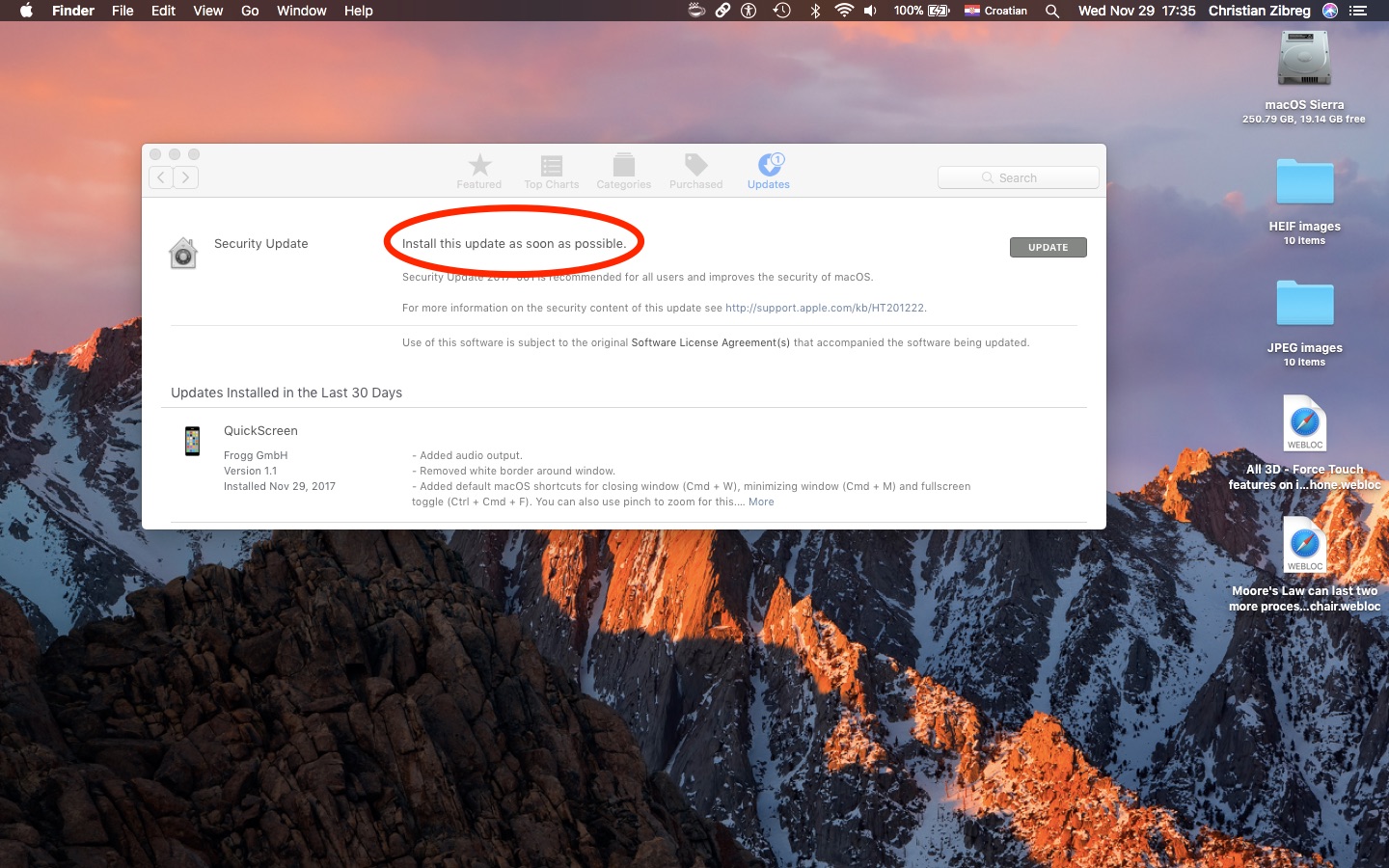
The patch is available for macOS High Sierra 10.13.1 or higher. Computers with macOS Sierra 10.12.6 or earlier are not impacted. To install this update, click the Updates tab in Mac App Store. No restart is required. Additional information on the security content of the Security Update 2017-001 is available in a support document on Apple’s website.
The Cupertino company also offered an apology to users, saying its customers “deserve better” and promising to audit its development process in order to prevent this from happening.
“We greatly regret this error and we apologize to all Mac users, both for releasing with this vulnerability and for the concern it has caused,” reads the statement. “Our customers deserve better. We are auditing our development process to help prevent this from happening again.”
After applying the patch, be sure that macOS’s build number is “17B1002” by selecting System Report → Software after choosing About This Mac from the Mac menu. If you require the root user account on your Mac, you can enable the root user and change its password.
Given the severity of this vulnerability, small wonder Apple is urging users to apply today’s patch as soon as possible to protect their privacy and strengthen the security of their Mac.