Mobile forensics firm Cellebrite that helped the United States Federal Bureau of Investigation bypass the passcode protection on the San Bernardino shooter’s iPhone 5c is adamant that it can also work around Apple’s security protections and hack into an iPhone 6, CNN reports.
Italian father Leonardo Fabbretti, who wanted to see the photos stored on his dead son Dama’s iPhone but was told by Apple that it was impossible to get into the device without a passcode, has now met with Cellebrite executives who have been working on accessing the files.
Grieving father turns to Cellebrite
“I just came back from their office in northern Italy. The meeting went well. They were able to download the directories with the iPhone’s content, but there is still work to be done in order to access the files,” Fabbretti said.
Dama didn’t use iCloud backup so Apple was unable to restore the photos, videos and messages on his phone. Although he had given his father Fabbretti access to his phone by registering his thumbprint, Fabbretti says the phone restarted.
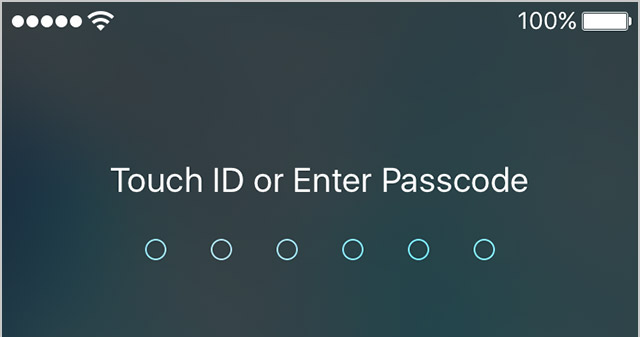
As Touch ID requires a passcode every time a device restarts, that has effectively prevented Fabbretti from getting into the phone as he doesn’t know his son’s passcode.
The myth of unhackable iPhones
Given Apple hasn’t shied away from marketing the strong security and encryption as one of the most important iPhone features setting it apart from the competition, the firm could suffer a major blow that could vastly change the public’s perception of iPhone security should Cellebrite successfully hack the iPhone 6.
Cellebrite was identified as the firm the FBI bought a tool from to bypass iOS 9’s passcode delay and automatic wipe features on the shooter’s iPhone 5c. Apple has said it was interested to learn about the exploits Cellebrite tapped in order to break into that device, but the FBI isn’t keen on sharing that information with the Cupertino firm.
Source: CNN