Watch our AirPods Pro 2 video tips explaining how to set up your earbuds, adjust touch controls, locate a lost charging case with Find My, charge it and more.
AirPods Pro 2 video tips: Adjusting swipe controls, ways to charge, Find My and more


Watch our AirPods Pro 2 video tips explaining how to set up your earbuds, adjust touch controls, locate a lost charging case with Find My, charge it and more.
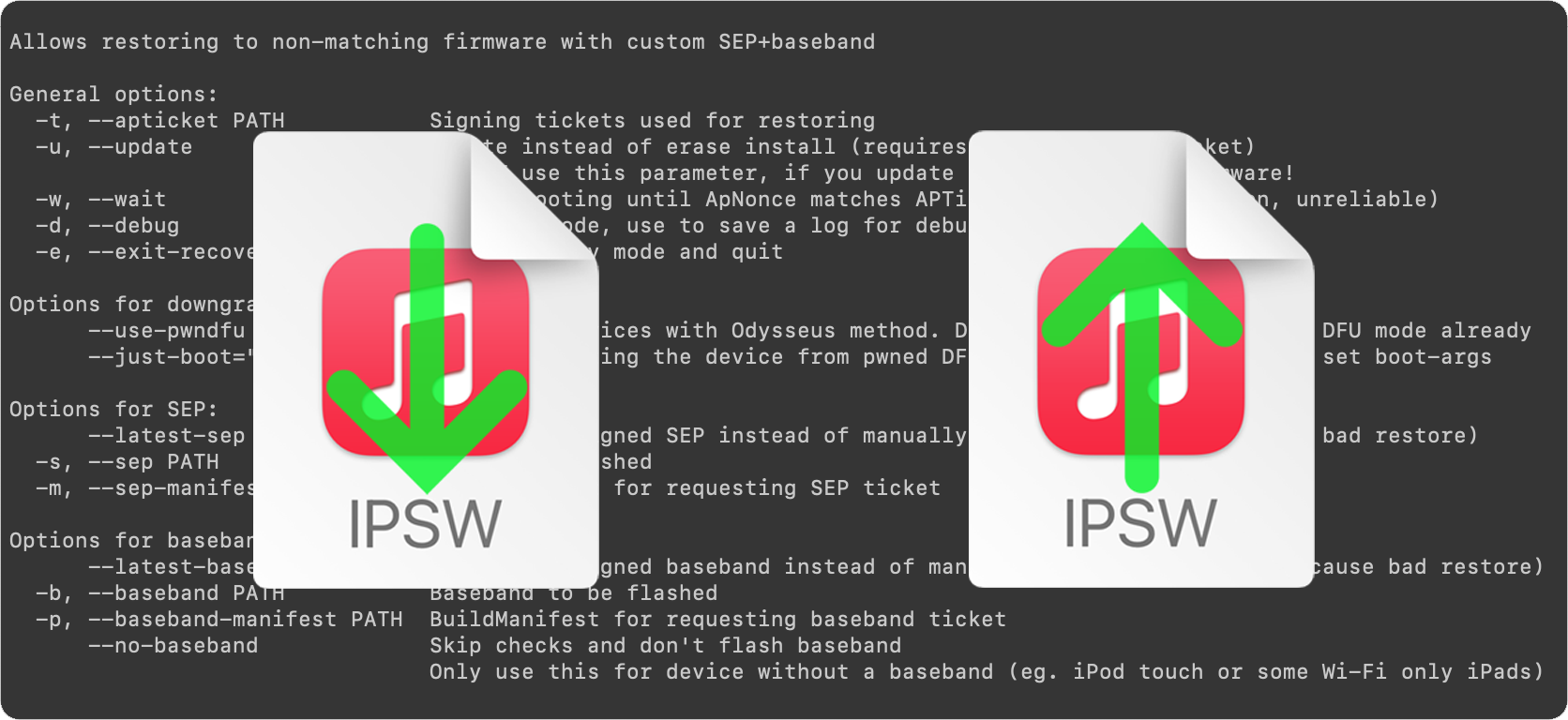
This is an introductory article which explains what futurerestore is and how it works, as well as how to follow our futurerestore guides to upgrade/downgrade your device.
Before attempting any of the guides, everyone should read this article. It explains whether the guides apply to you, and if they do, which ones you should follow, as well as making sure that you fulfil the requirements for it to work. Not everyone can use futurerestore.
This is Part 1 of a two-part guide on how to use futurerestore.
Before attempting this guide, everyone should read the introductory article, Guide to futurerestore: Introduction. It will explain whether this guide applies to you, as well as making sure that you fulfil the requirements for it to work.
If you currently have a jailbreak and you want to move to a different firmware with futurerestore’s generator mode, you must follow this guide first before following Part 2.
If you currently have no jailbreak, and you want to move to a different firmware with futurerestore’s Apnonce collision mode, you can skip this guide and head straight to Part 2. This method does not apply to most users.
This is Part 2 of a two-part guide on how to use futurerestore.
Before attempting this guide, everyone should read the introductory article, Guide to futurerestore: Introduction. This will explain whether the guides apply to you, as well as making sure that you fulfil the requirements for it to work.
If you currently have a jailbreak and you want to move to a different firmware with futurerestore's generator mode, you must follow Part 1 of the guide before following Part 2.
If you currently have no jailbreak, and you want to move to a different firmware with futurerestore's Apnonce collision mode, do only this part of the guide. This method does not apply to most users.
On Monday, we reported on Apple's point update release of iOS 12.5.1 for older devices which cannot run iOS 13 and higher. The only stated change in the update was a fix for a bug in the COVID-19 exposure notifications feature, which Apple had previously added to older firmwares to allow more device owners to make use of it.
Although the release notes didn't mention any other changes, it would not have been unusual for Apple to have taken the opportunity to patch the vulnerabilities used by iOS 12.x jailbreaks, such as the Chimera jailbreak for iOS 12-12.5. The update could also have rendered the jailbreak tool unusable accidentally. Unrelated changes in the firmware, or hard-coded firmware support in the Chimera app itself, could also have required an update to the tool for it to work again.
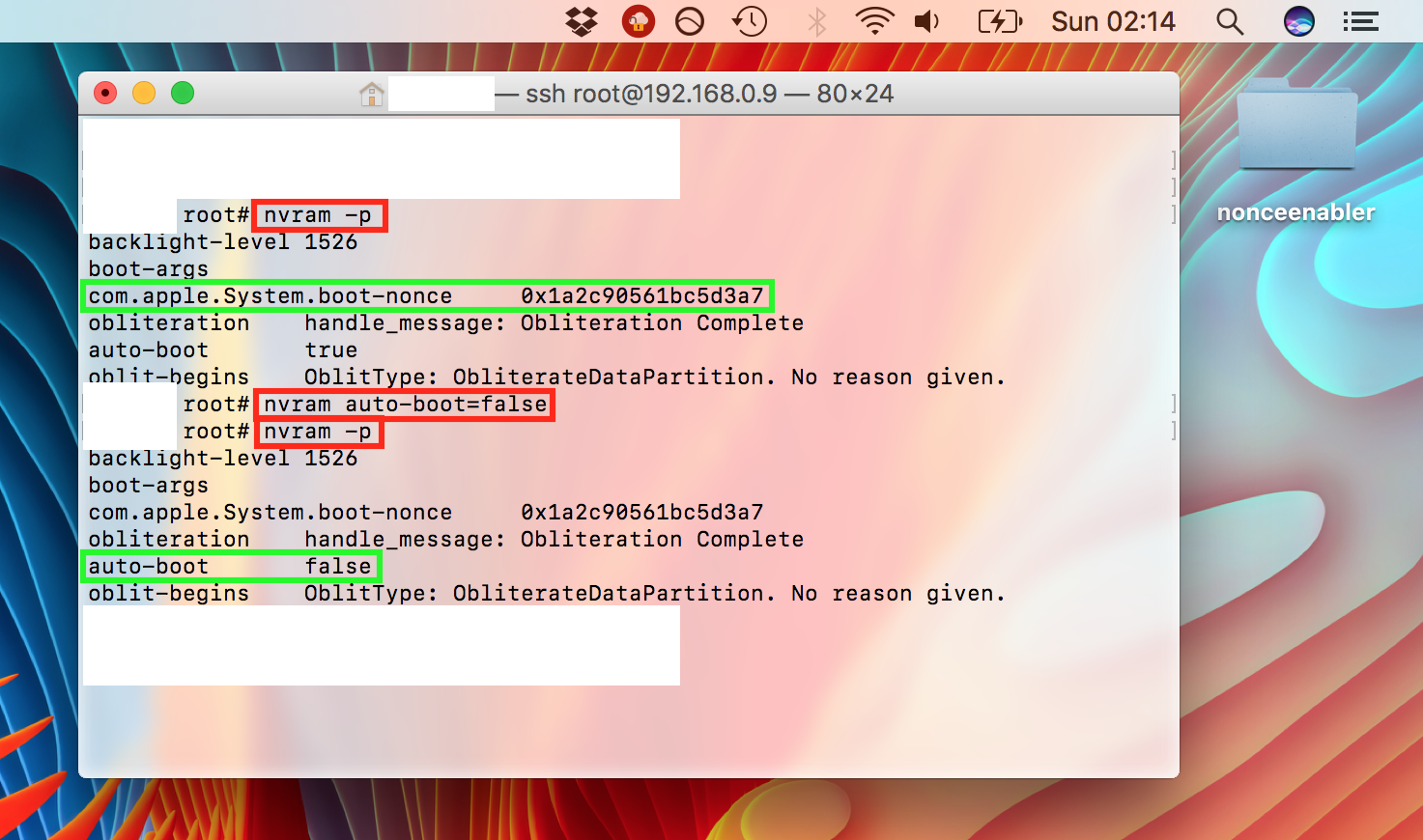
First off, this guide is only necessary for 64-bit devices which are currently jailbroken on old firmwares, such as iOS 9 and some versions of iOS 10. The jailbreaks for those firmwares did not always include a way to set a generator for use with futurerestore, and nonceEnabler provides that ability. Nearly all newer jailbreaks provide their own simpler ways of setting a generator, and they do not need to use nonceEnabler, nor this guide. If your device is not currently jailbroken on an old firmware such as the ones mentioned in this guide, and/or has its own method of setting a generator, refer instead to our main futurerestore guides.
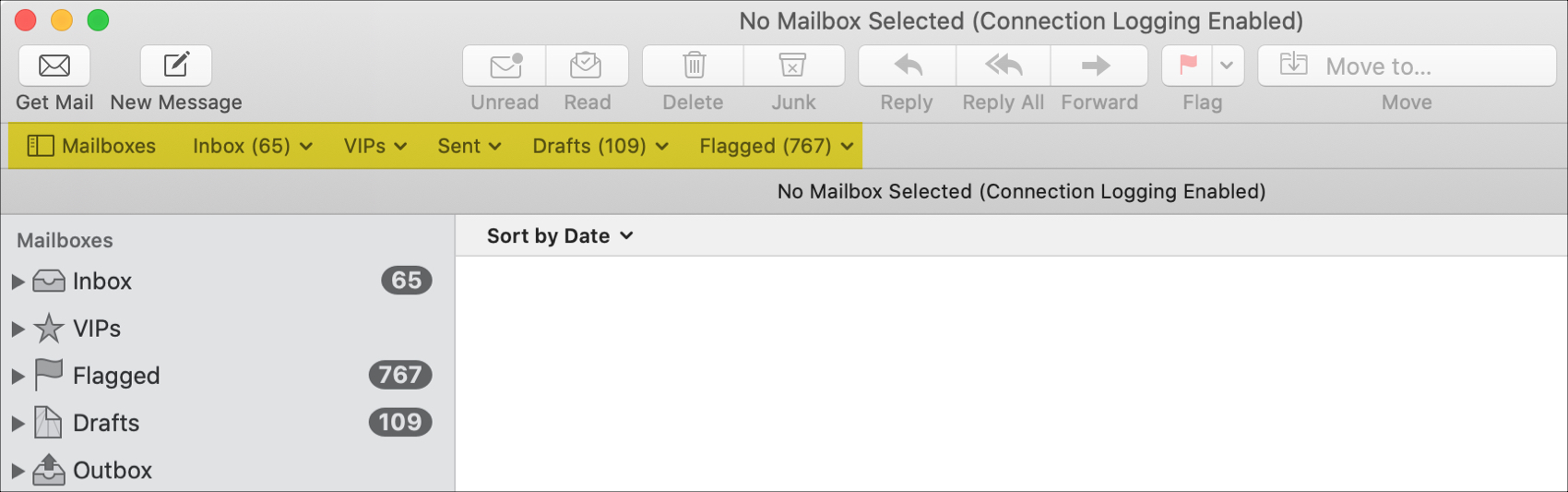
If you simply haven’t spent much time with the Mail app on your Mac, then you may be missing out on the use of a handy tool.
The Favorites Bar in the Mail app is a nice spot to see your most-used Mailboxes, help with searches, and open and close your Mailbox list. Here, we’ll explain what the Favorites Bar is in Mac Mail and ways you can use it.
Setapp is a subscription service aimed at Mac users created by MacPaw Inc. The service provides access to more than 160 applications for $9.99 per month. Up until now, only individual memberships have been available. Starting today, though, MacPaw is offering Setapp for Teams. The company is providing early access to the new teams feature as a public beta.

With no USB-C port to connect it to a computer, the Apple TV 4K falls firmly into the category of "irksome products which Apple doesn't want you to mess with". However, although it is easier to get your own apps onto its older brother the Apple TV 4, it's still possible to sign and sideload apps on the 4K.
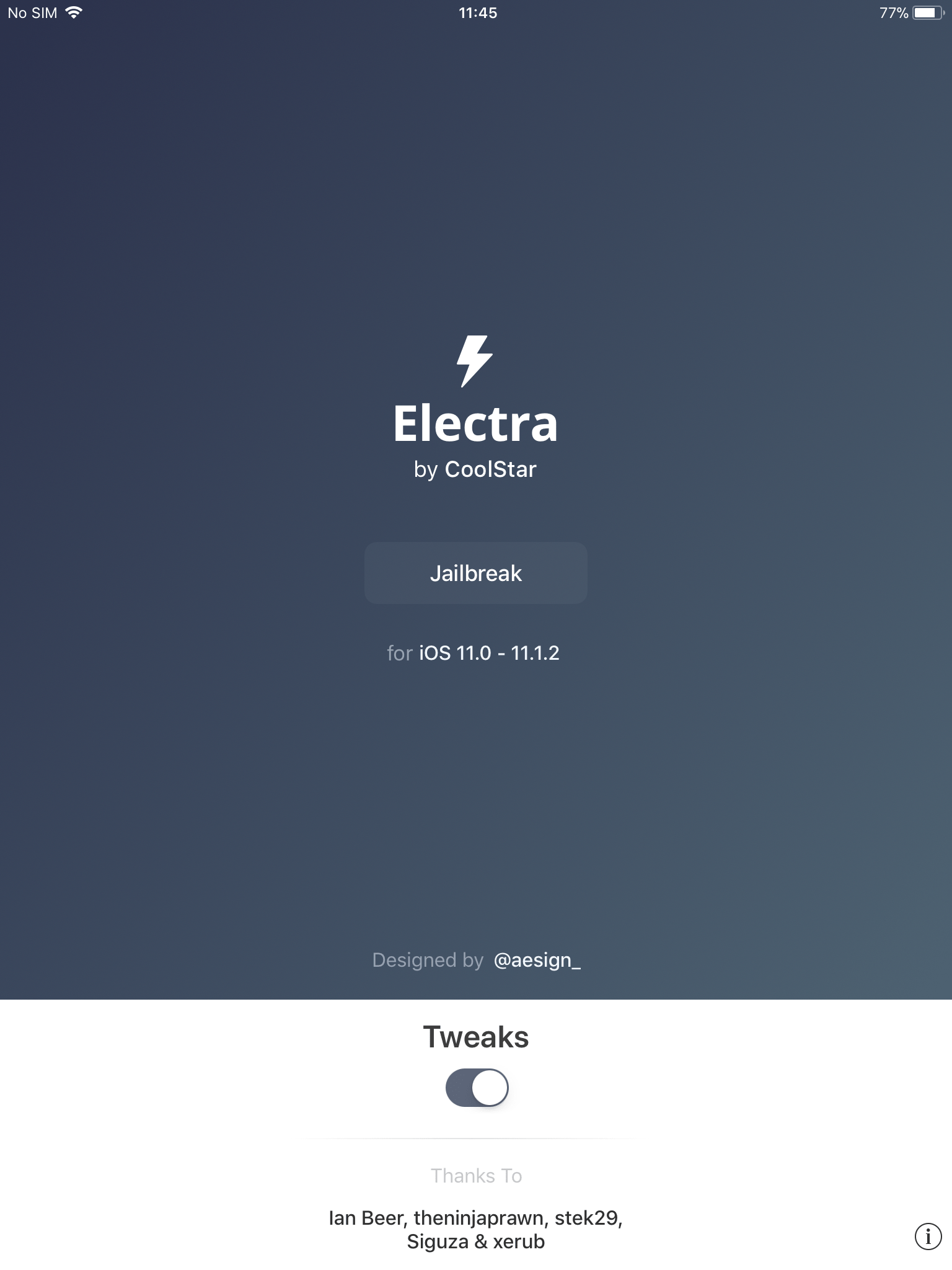
Electra for iOS 11.0-11.3.1 is out and in wide use. It seems to work very smoothly for most, perhaps due to the extensive beta period, but it isn't without some reported problems. Add to that the rumor of a more traditional alternative from Saurik et al. and you could be forgiven for deciding to wait it out a while.

You may have been following our coverage of Electra's progress through beta phase to release candidate, as it acquires the requisite functionality to be considered a full end-user jailbreak. With the addition of Cydia to the tool it became clear that a full release was not far off, and sure enough, today saw version 1.0 (and afterwards 1.0.1) posted to the official website.

A few days ago we wrote about the release of nitoTV, Kevin Bradley's package manager for jailbroken Apple TVs. Today, we'll give you an in-depth look at the interface and functionality, as well as our comments on where it could go in the future.