In this guide, we will go over important tips to help secure your Gmail, YouTube, and other Google accounts, keeping your personal data as safe as possible.
How to secure your Google account and prevent unauthorized access


In this guide, we will go over important tips to help secure your Gmail, YouTube, and other Google accounts, keeping your personal data as safe as possible.

Learn how to create a PlayStation passkey, which allows you to log in to your Sony PlayStation Network account with Face ID and Touch ID instead of the password.

As promised back in February, Dopamine and TrollStore lead developer Lars Fröder (@opa334dev) took the stage at Zer0con 2024, a high-level and closed conference about software security, to discuss a technical deep dive about jailbreaking iOS 16.
In this tutorial, we will show you how to activate the new Stolen Device Protection feature on your iPhone. This will protect your Apple ID, account passwords, and other critical personal information when your device is stolen or in an unfamiliar location.
If you've encountered issues using USB hubs, Java software or professional audio plug-ins on your Mac, installing macOS Sonoma 14.41 should fix them.

Do you have reasons to believe your Facebook account has been compromised? In this guide, we will show you how to see if someone is using your Facebook account and share essential tips to secure it from further unauthorized access.
Although iOS 17.4.1 doesn't introduce any new features, you're recommended to install it to get Apple's latest security patches protecting against threats.

Getting locked out of your computer could easily be one of the most frustrating things that could happen to you. This guide shares a few useful tips that will ensure you do not face this issue on your Mac.
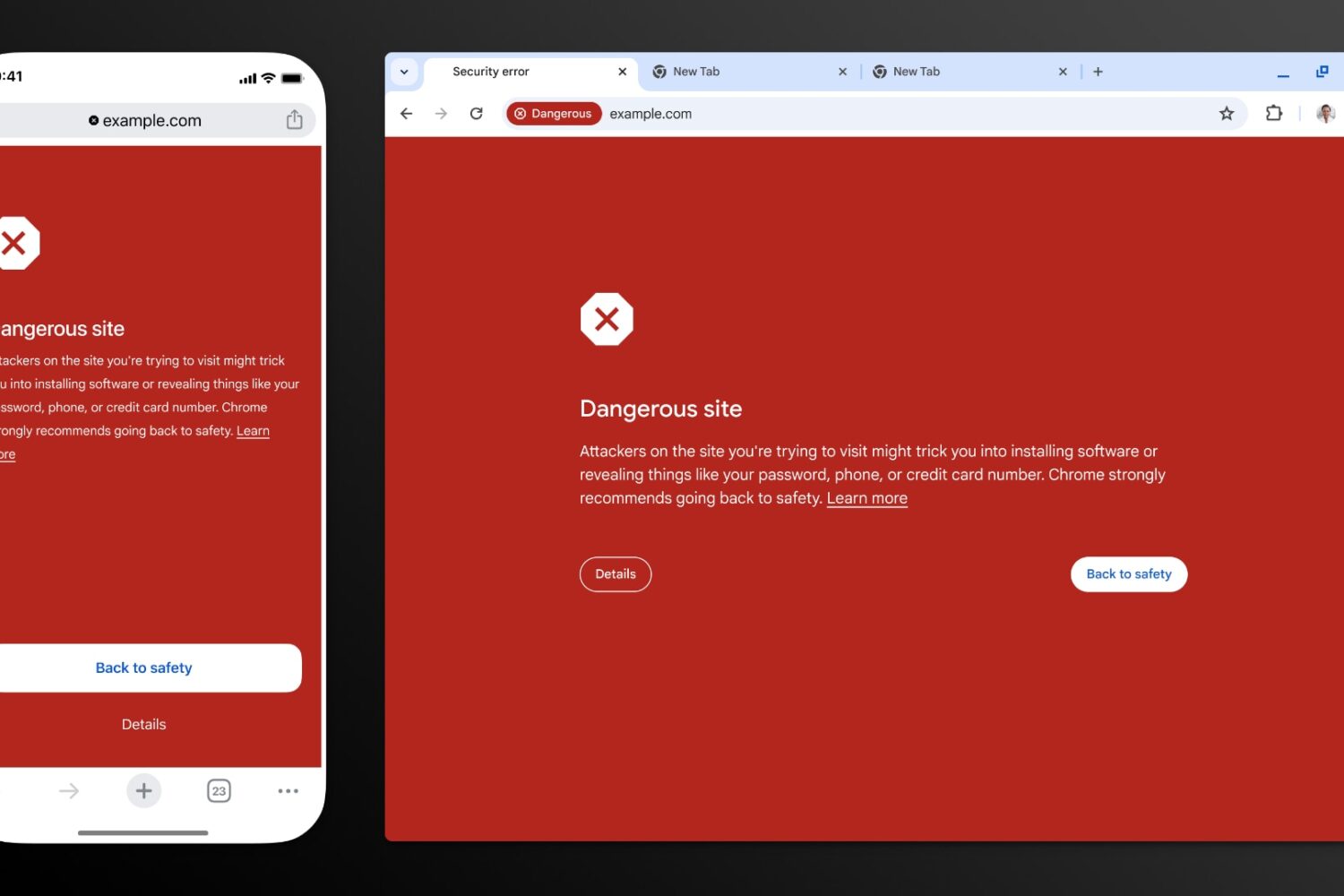
Thanks to recent improvements such as real-time checks, Google Chrome’s Safe Browsing feature now blocks 25 percent more phishing attempts.

Some time ago, iOS developer and unc0ver jailbreak lead developer pwn20wnd released an app in the App Store called Unveil that could display device information and check for software modifications on said device.

Lots of people who hold iPhone jailbreaking near and dear to their hearts remember the sinking feeling they felt when Apple announced that iOS 17 wouldn’t run on the iPhone X and older devices. This decision effectively ended the use of the checkm8 exploit to jailbreak any iPhone firmware newer than iOS 16.
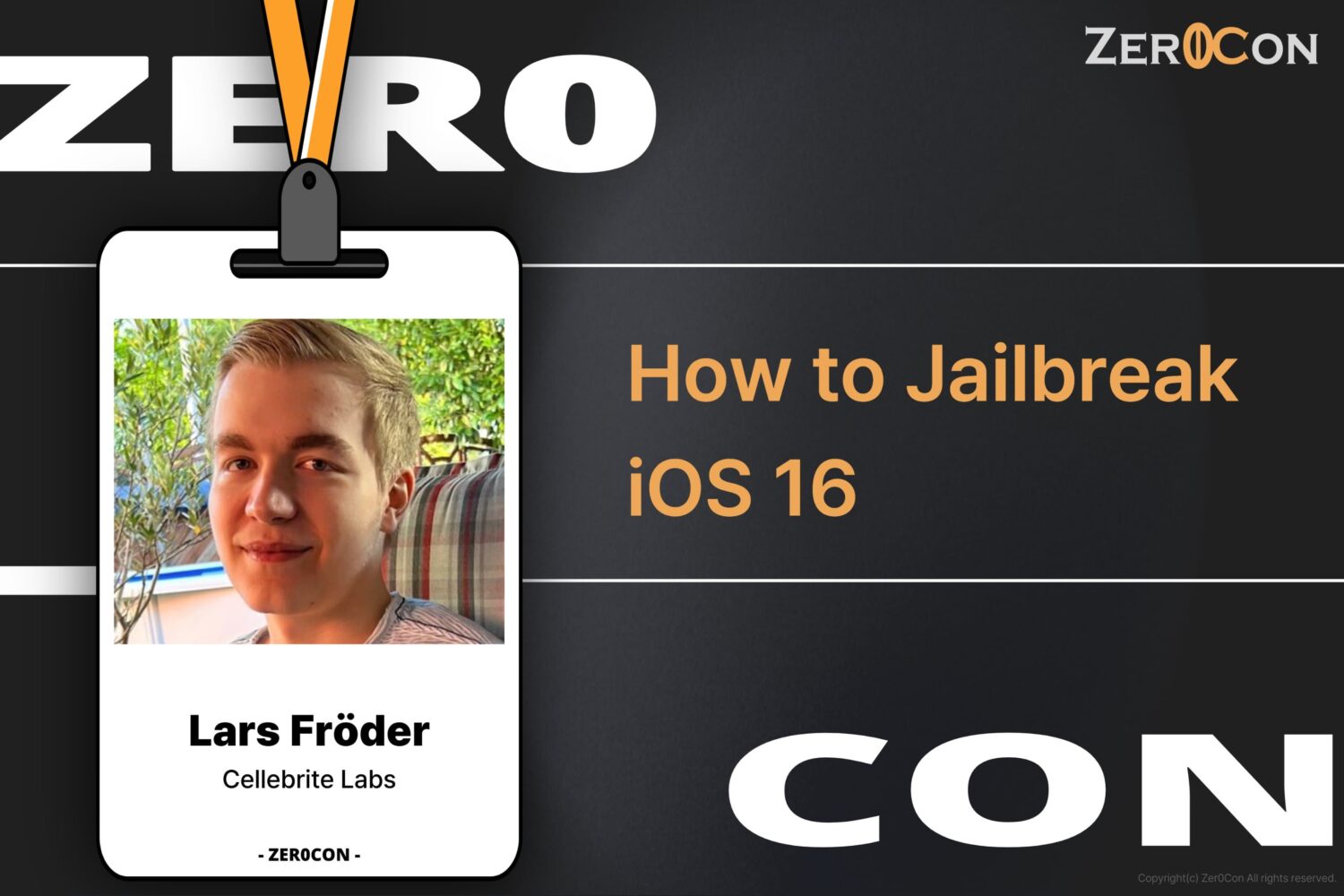
If you, like so many other jailbreakers, enjoy the experience of listening to jailbreak makers speak at special events, then you might be interested in knowing that Dopamine jailbreak lead developer Lars Fröder (@opa334dev) will give a talk at Zer0con 2024.