
On March 29, 2018, Apple released the watchOS 4.3 software update for Apple Watch. Among other improvements and fixes, watchOS 4.3 reinstates the ability to browse music on your paired iPhone via your wrist while enabling new features like portrait Nightstand mode.
watchOS 4.3 is available for all Apple Watch models.
To update your device to watchOS 4.3, go to My Watch → General → Software Update in the companion Watch app on your paired iPhone. To install the update, the watch must be placed on its charging disk, have at least 50 percent battery and be in range of your iPhone.
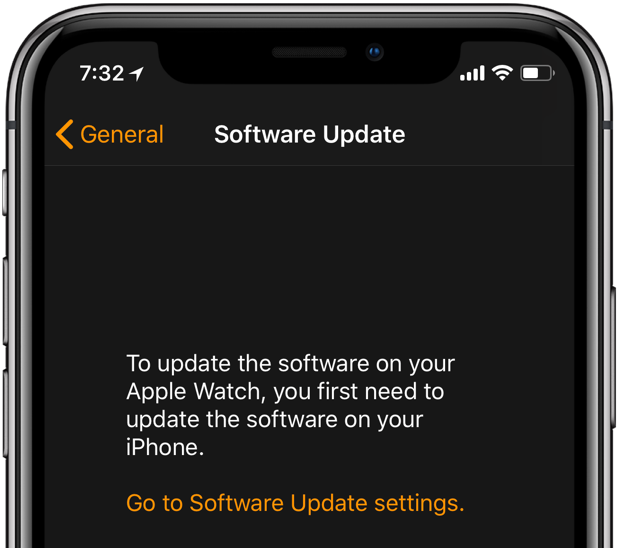
iPhone must be running iOS 11.3 or later for watchOS 4.3 to show up as an update.
The introduction of portrait Nightstand mode is a great little tweak. Before watchOS 4.3, your watch needed to be laid on a charger horizontally in order to use Nightstand mode.
With watchOS 4.3 and later, this feature is now available in either vertical or horizontal orientation, which is especially great if you’re looking to rest your watch on Apple’s AirPower charger or another Qi wireless charging mat.

Nightstand mode is now accessible in portrait orientation, too
Here’s everything included in the watchOS 4.3 update.
watchOS 4.3 release notes
This update contains new features, improvements and bug fixes.
- Control volume and playback on HomePod from your Apple Watch
- Send audio from iPhone to AirPlay speakers from your Apple Watch
- Apple Watch” now reads as “Speaker“ in AirPlay menu within Control Center
- Restores ability to control music on iPhone via Music app on your Apple Watch
- Use any orientation for Nightstand charging mode
- New charging animation when you rest your Apple Watch on its charger
- Fixes an issue where Siri music commands were not working for some audio devices
- Resolves an issue where Activity achievements were incorrectly awarded for some users
- Siri watch face now shows progress towards closing Activity rings and when new songs are added to Apple Music mixes
Watch our video walkthrough of all the major changes in watchOS 4.3, embedded below.
Subscribe to iDownloadBlog on YouTube
Visit Apple’s website for more information on watchOS updates.
watchOS 4.3 security fixes
watchOS 4.3 fixes the following vulnerabilities:
CoreFoundation
- Available for: All Apple Watch models
- Impact: An application may be able to gain elevated privileges
- Description: A race condition was addressed with additional validation.
- CVE-2018-4155: Samuel Groß (@5aelo)
- CVE-2018-4158: Samuel Groß (@5aelo)
CoreText
- Available for: All Apple Watch models
- Impact: Processing a maliciously crafted string may lead to a denial of service
- Description: A denial of service issue was addressed through improved memory handling.
- CVE-2018-4142: Robin Leroy of Google Switzerland GmbH
File System Events
- Available for: All Apple Watch models
- Impact: An application may be able to gain elevated privileges
- Description: A race condition was addressed with additional validation.
- CVE-2018-4167: Samuel Groß (@5aelo)
Kernel
- Available for: All Apple Watch models
- Impact: A malicious application may be able to execute arbitrary code with kernel privileges
- Description: Multiple memory corruption issues were addressed with improved memory handling.
- CVE-2018-4150: an anonymous researcher
Kernel
- Available for: All Apple Watch models
- Impact: An application may be able to read restricted memory
- Description: A validation issue was addressed with improved input sanitization.
- CVE-2018-4104: The UK’s National Cyber Security Centre (NCSC)
Kernel
- Available for: All Apple Watch models
- Impact: An application may be able to execute arbitrary code with kernel privileges
- Description: A memory corruption issue was addressed with improved memory handling.
- CVE-2018-4143: derrek (@derrekr6)
NSURLSession
- Available for: All Apple Watch models
- Impact: An application may be able to gain elevated privileges
- Description: A race condition was addressed with additional validation.
- CVE-2018-4166: Samuel Groß (@5aelo)
Quick Look
- Available for: All Apple Watch models
- Impact: An application may be able to gain elevated privileges
- Description: A race condition was addressed with additional validation.
- CVE-2018-4157: Samuel Groß (@5aelo)
Security
- Available for: All Apple Watch models
- Impact: A malicious application may be able to elevate privileges
- Description: A buffer overflow was addressed with improved size validation.
- CVE-2018-4144: Abraham Masri (@cheesecakeufo)
System Preferences
- Available for: All Apple Watch models
- Impact: A configuration profile may incorrectly remain in effect after removal
- Description: An issue existed in CFPreferences. This issue was addressed through improved preferences cleanup.
- CVE-2018-4115: Johann Thalakada, Vladimir Zubkov, and Matt Vlasach of Wandera
WebKit
- Available for: All Apple Watch models
- Impact: Unexpected interaction with indexing types causing an ASSERT failure
- Description: An array indexing issue existed in the handling of a function in javascript core. This issue was addressed through improved checks.
- CVE-2018-4113: found by OSS-Fuzz
WebKit
- Available for: All Apple Watch models
- Impact: Processing maliciously crafted web content may lead to a denial of service
- Description: A memory corruption issue was addressed through improved input validation.
- CVE-2018-4146: found by OSS-Fuzz
WebKit
- Available for: All Apple Watch models
- Impact: Processing maliciously crafted web content may lead to arbitrary code execution
- Description: Multiple memory corruption issues were addressed with improved memory handling.
- CVE-2018-4114: found by OSS-Fuzz
- CVE-2018-4121: Natalie Silvanovich of Google Project Zero
- CVE-2018-4122: WanderingGlitch of Trend Micro’s Zero Day Initiative
- CVE-2018-4125: WanderingGlitch of Trend Micro’s Zero Day Initiative
- CVE-2018-4129: likemeng of Baidu Security Lab working with Trend Micro’s Zero Day Initiative
- CVE-2018-4161: WanderingGlitch of Trend Micro’s Zero Day Initiative
- CVE-2018-4162: WanderingGlitch of Trend Micro’s Zero Day Initiative
- CVE-2018-4163: WanderingGlitch of Trend Micro’s Zero Day Initiative
WebKit
- Available for: All Apple Watch models
- Impact: A malicious website may exfiltrate data cross-origin
- Description: A cross-origin issue existed with the fetch API. This was addressed through improved input validation.
- CVE-2018-4117: an anonymous researcher, an anonymous researcher
To learn more about the security content of watchOS 4.3, read Apple’s support document. For further details regarding security updates for all Apple software, visit their website.
Keep in mind that some Apple Watch features may be unavailable in some countries or areas. For more information on that, visit Apple’s watchOS Feature Availability webpage.